Upgrade & Secure Your Future with DevOps, SRE, DevSecOps, MLOps!
We spend hours scrolling social media and waste money on things we forget, but won’t spend 30 minutes a day earning certifications that can change our lives.
Master in DevOps, SRE, DevSecOps & MLOps by DevOps School!
Learn from Guru Rajesh Kumar and double your salary in just one year.
Introduction
Deception Technology Tools are security solutions that detect, analyze, and respond to threats by luring attackers into decoy systems, assets, or networks. In plain English, these tools create traps or honeypots that look like legitimate targets to attackers, allowing organizations to identify intrusions and study attacker behavior without exposing real assets. Unlike traditional security tools, deception technology focuses on early detection and proactive threat mitigation.
In and beyond, deception technology is increasingly critical due to the rise of sophisticated cyberattacks, insider threats, and ransomware. Organizations adopting hybrid cloud, remote work models, and complex IT environments require advanced detection mechanisms to complement conventional firewalls, IDS, and endpoint security.
Real-world use cases include:
- Detecting advanced persistent threats (APTs) before critical systems are compromised.
- Monitoring insider threats and compromised credentials.
- Validating the effectiveness of existing security controls.
- Early detection of lateral movement within networks.
- Testing incident response procedures and threat hunting.
Key criteria buyers should evaluate:
- Realistic decoy creation and customization.
- Automated alerting and response.
- Integration with SIEM, SOAR, and threat intelligence platforms.
- Coverage across endpoints, cloud, network, and applications.
- Ease of deployment and scalability for enterprise environments.
- Reporting, analytics, and forensic capabilities.
- AI-powered attack pattern recognition.
- Compliance support and audit readiness.
- Licensing and subscription flexibility.
Best for: Security operations centers (SOCs), threat intelligence teams, IT security professionals, and enterprises with high-value data assets or regulatory requirements.
Not ideal for: Small businesses with limited IT infrastructure or minimal attack surface, where conventional security tools may suffice.
Key Trends in Deception Technology Tools
- AI-Driven Threat Detection: Leveraging machine learning to recognize attacker behaviors and patterns in real-time.
- Cloud-Native Decoy Deployment: Deploying honeypots and deception assets in hybrid or multi-cloud environments.
- Integration with SOAR and SIEM: Streamlined alerts, automated responses, and forensic data collection.
- Adaptive Deception: Dynamically updating decoy systems based on network changes or attacker behavior.
- IoT and OT Security Coverage: Expanding deception to industrial and IoT devices.
- Insider Threat Detection: Identifying unusual internal user behavior.
- Behavioral Analytics and Threat Intelligence: Leveraging attacker interaction data to refine security policies.
- Micro-Segmentation Support: Preventing lateral movement by combining deception with network segmentation.
- Compliance and Audit Integration: Supporting GDPR, HIPAA, SOC 2, and other regulatory standards.
- Subscription and Usage-Based Models: Flexible licensing for SMBs and enterprises.
How We Selected These Tools (Methodology)
- Evaluated market adoption and mindshare among SOC teams and cybersecurity professionals.
- Assessed feature completeness including decoy creation, alerting, and response automation.
- Reviewed reliability and performance signals such as deployment stability and alert accuracy.
- Analyzed integration capabilities with SIEM, SOAR, and threat intelligence platforms.
- Evaluated security posture including SSO, MFA, encryption, and audit logging.
- Considered customer fit across SMB, mid-market, and enterprise organizations.
- Reviewed AI-driven detection, analytics, and adaptive decoy capabilities.
- Assessed scalability for distributed and hybrid IT environments.
- Considered vendor support, documentation, and community engagement.
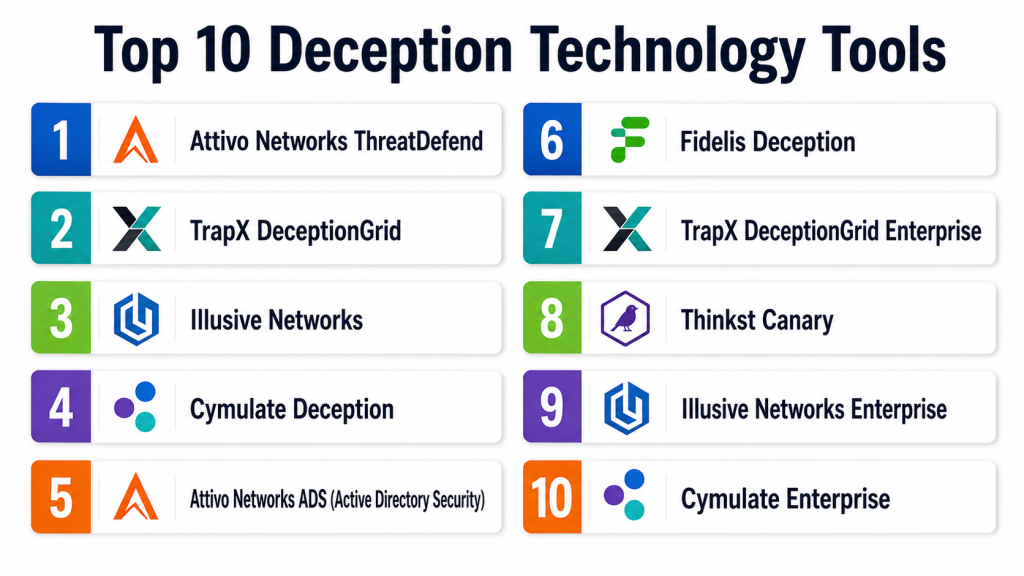
Top 10 Deception Technology Tools
#1 — Attivo Networks ThreatDefend
Short description: ThreatDefend deploys decoys, lures, and traps across endpoints, networks, and cloud assets, enabling early threat detection and attacker behavior analysis. Ideal for enterprises seeking proactive SOC visibility.
Key Features
- Endpoint and network decoys.
- Real-time alerting and response.
- Identity threat detection.
- Integration with SIEM/SOAR.
- Behavioral analytics.
Pros
- Early threat detection.
- Reduces dwell time for attackers.
Cons
- Premium pricing.
- Requires SOC expertise for full utilization.
Platforms / Deployment
- Windows / Linux / macOS / Web.
- Cloud / Self-hosted / Hybrid.
Security & Compliance
- SSO/MFA, encryption.
- SOC 2, ISO 27001, GDPR supported.
Integrations & Ecosystem
- Integrates with Splunk, IBM QRadar, and SOAR platforms.
- API access for automation.
- Supports hybrid IT and cloud.
Support & Community
- Vendor support included.
- Documentation, training, and webinars.
#2 — TrapX DeceptionGrid
Short description: DeceptionGrid creates decoys, traps, and lures to detect advanced threats, insider attacks, and ransomware. Suitable for enterprises needing early detection and forensic analysis.
Key Features
- Automated decoy deployment.
- Ransomware detection and alerting.
- Network-wide honeypots.
- Centralized dashboard.
- Integration with SOC tools.
Pros
- Strong attack simulation.
- Realistic decoy assets.
Cons
- Complexity for SMBs.
- Premium pricing.
Platforms / Deployment
- Windows / Linux / Web.
- Cloud / On-premises.
Security & Compliance
- SSO/MFA, encryption.
- GDPR, SOC 2, ISO 27001.
Integrations & Ecosystem
- SIEM, SOAR, and threat intelligence platforms.
- API support for automation.
- Hybrid network support.
Support & Community
- Vendor support available.
- Training and documentation.
#3 — Illusive Networks
Short description: Illusive Networks provides endpoint and network deception for early threat detection and mitigation, with behavioral analytics to track attackers’ lateral movement.
Key Features
- Endpoint decoys and fake credentials.
- Network traps and lures.
- Behavioral threat analytics.
- Automated alerts and remediation.
- Integration with SOC and SIEM.
Pros
- Reduces attacker dwell time.
- Realistic decoy deployments.
Cons
- Enterprise-focused pricing.
- Learning curve for small teams.
Platforms / Deployment
- Windows / Linux / macOS.
- Cloud / Hybrid.
Security & Compliance
- SSO/MFA, encryption.
- SOC 2, GDPR.
Integrations & Ecosystem
- Integrates with Splunk, IBM QRadar, SOAR platforms.
- API access for custom automation.
- Supports hybrid networks.
Support & Community
- Vendor support included.
- Documentation and webinars.
#4 — Cymulate Deception
Short description: Cymulate Deception provides automated decoy deployment, attack path simulation, and threat detection for enterprises and security teams.
Key Features
- Automated decoy and honeypot setup.
- Continuous attack simulation.
- Threat path analytics.
- Centralized monitoring dashboard.
- Integration with SOC tools.
Pros
- Quick deployment and automation.
- Actionable analytics for SOC teams.
Cons
- Limited free-tier options.
- Enterprise features require licensing.
Platforms / Deployment
- Windows / Linux / Web.
- Cloud.
Security & Compliance
- SSO/MFA, encryption.
- SOC 2, ISO 27001.
Integrations & Ecosystem
- Integrates with SIEM, SOAR, cloud monitoring tools.
- API support for automated workflows.
- Supports hybrid IT environments.
Support & Community
- Vendor support available.
- Knowledge base and documentation.
#5 — Attivo Networks ADS (Active Directory Security)
Short description: ADS integrates deception for Active Directory environments, detecting lateral movement, credential theft, and insider threats.
Key Features
- Fake credentials and honey accounts.
- Active Directory monitoring.
- Lateral movement detection.
- Centralized alerting.
- Integration with SIEM.
Pros
- Focused on identity attacks.
- Early detection of insider threats.
Cons
- Specialized deployment for AD environments.
- Enterprise pricing.
Platforms / Deployment
- Windows / Web.
- Cloud / On-premises.
Security & Compliance
- SSO/MFA, encryption.
- SOC 2, GDPR.
Integrations & Ecosystem
- SIEM, SOAR integration.
- API access for automation.
- Compatible with hybrid networks.
Support & Community
- Vendor support included.
- Training and documentation.
#6 — Fidelis Deception
Short description: Fidelis Deception delivers decoys, traps, and deception-based threat detection for enterprise networks and cloud environments, enabling early detection of breaches.
Key Features
- Endpoint and network decoys.
- Ransomware and malware detection.
- Behavioral analytics.
- Centralized dashboard.
- Integration with security tools.
Pros
- Rapid breach detection.
- Realistic attack simulation.
Cons
- Premium pricing.
- Complex deployment for smaller teams.
Platforms / Deployment
- Windows / Linux / Web.
- Cloud / Hybrid.
Security & Compliance
- SSO/MFA, encryption.
- SOC 2, ISO 27001, GDPR.
Integrations & Ecosystem
- SIEM, SOAR, threat intelligence platforms.
- API access for automation.
- Hybrid network support.
Support & Community
- Vendor support included.
- Documentation and webinars.
#7 — TrapX DeceptionGrid Enterprise
Short description: Advanced enterprise version of TrapX, designed for large-scale deception deployment across networks and endpoints.
Key Features
- Enterprise-scale decoys and lures.
- Automated alerts and remediation.
- Integration with SOC and SIEM.
- Behavioral analytics.
- Reporting and dashboards.
Pros
- Large-scale deployment support.
- Advanced attack simulation.
Cons
- High complexity and cost.
- Requires experienced SOC staff.
Platforms / Deployment
- Windows / Linux / Web.
- Cloud / Hybrid.
Security & Compliance
- SSO/MFA, encryption.
- SOC 2, ISO 27001, GDPR.
Integrations & Ecosystem
- SIEM, SOAR, endpoint integration.
- API access.
- Hybrid cloud support.
Support & Community
- Vendor support included.
- Documentation and training.
#8 — Thinkst Canary
Short description: Thinkst Canary provides simple, effective deception for networks by deploying decoy systems to detect intrusions and attacks early.
Key Features
- Lightweight honeypots.
- Automated alerting.
- Easy-to-deploy sensors.
- Behavioral monitoring.
- Dashboard reporting.
Pros
- Simple deployment and management.
- Effective early detection.
Cons
- Limited advanced analytics.
- Best suited for SMB to mid-market.
Platforms / Deployment
- Windows / Linux / Web.
- Cloud / On-premises.
Security & Compliance
- SSO/MFA, encryption.
- SOC 2, GDPR support.
Integrations & Ecosystem
- SIEM integration.
- API support for automation.
- Hybrid network compatible.
Support & Community
- Vendor support included.
- Documentation and community forums.
#9 — Illusive Networks Enterprise
Short description: Enterprise-focused Illusive Networks provides advanced deception to prevent lateral movement and detect insider threats in large networks.
Key Features
- Endpoint decoys and fake credentials.
- Lateral movement detection.
- Identity threat analytics.
- Centralized alerting.
- SIEM integration.
Pros
- Strong insider threat detection.
- Effective enterprise-scale deployment.
Cons
- High cost for SMBs.
- Requires trained SOC teams.
Platforms / Deployment
- Windows / Linux / macOS.
- Cloud / Hybrid.
Security & Compliance
- SSO/MFA, encryption.
- SOC 2, GDPR.
Integrations & Ecosystem
- SIEM and SOAR integration.
- API access.
- Supports hybrid IT.
Support & Community
- Vendor support included.
- Training and documentation.
#10 — Cymulate Enterprise
Short description: Cymulate Enterprise provides deception and attack simulation across networks and cloud, helping enterprises proactively detect threats.
Key Features
- Automated decoy deployment.
- Attack path simulation.
- Behavioral analytics.
- Centralized monitoring.
- SOC integration.
Pros
- Continuous threat detection.
- Supports large-scale enterprise networks.
Cons
- Premium pricing.
- Setup requires IT expertise.
Platforms / Deployment
- Windows / Linux / Web.
- Cloud / Hybrid.
Security & Compliance
- SSO/MFA, encryption.
- SOC 2, ISO 27001, GDPR.
Integrations & Ecosystem
- SIEM, SOAR, threat intelligence.
- API support for automation.
- Hybrid network and cloud compatible.
Support & Community
- Vendor support included.
- Documentation, webinars, and knowledge base.
Comparison Table (Top 10)
| Tool Name | Best For | Platform(s) Supported | Deployment | Standout Feature | Public Rating |
|---|---|---|---|---|---|
| Attivo Networks ThreatDefend | Enterprise | Windows / Linux / macOS / Web | Cloud / Self-hosted / Hybrid | Real-time decoy alerts | N/A |
| TrapX DeceptionGrid | Enterprise | Windows / Linux / Web | Cloud / On-premises | Automated decoy deployment | N/A |
| Illusive Networks | Enterprise | Windows / Linux / macOS | Cloud / Hybrid | Endpoint decoys & lateral movement detection | N/A |
| Cymulate Deception | Enterprise | Windows / Linux / Web | Cloud | Continuous attack simulation | N/A |
| Attivo Networks ADS | Enterprise | Windows / Web | Cloud / On-premises | Active Directory deception | N/A |
| Fidelis Deception | Enterprise | Windows / Linux / Web | Cloud / Hybrid | Rapid breach detection | N/A |
| TrapX DeceptionGrid Enterprise | Enterprise | Windows / Linux / Web | Cloud / Hybrid | Large-scale decoy deployment | N/A |
| Thinkst Canary | SMB / Mid-market | Windows / Linux / Web | Cloud / On-premises | Lightweight honeypots | N/A |
| Illusive Networks Enterprise | Enterprise | Windows / Linux / macOS | Cloud / Hybrid | Insider threat detection | N/A |
| Cymulate Enterprise | Enterprise | Windows / Linux / Web | Cloud / Hybrid | Enterprise attack simulation | N/A |
Evaluation & Scoring of Deception Technology Tools
| Tool Name | Core (25%) | Ease (15%) | Integrations (15%) | Security (10%) | Performance (10%) | Support (10%) | Value (15%) | Weighted Total |
|---|---|---|---|---|---|---|---|---|
| Attivo Networks ThreatDefend | 9 | 8 | 8 | 9 | 9 | 8 | 7 | 8.3 |
| TrapX DeceptionGrid | 8 | 7 | 8 | 9 | 8 | 7 | 7 | 7.8 |
| Illusive Networks | 8 | 7 | 8 | 9 | 8 | 7 | 7 | 7.8 |
| Cymulate Deception | 8 | 8 | 7 | 9 | 8 | 7 | 7 | 7.8 |
| Attivo Networks ADS | 8 | 7 | 8 | 9 | 8 | 7 | 7 | 7.8 |
| Fidelis Deception | 8 | 7 | 8 | 9 | 8 | 7 | 7 | 7.8 |
| TrapX DeceptionGrid Enterprise | 8 | 7 | 8 | 9 | 8 | 7 | 7 | 7.8 |
| Thinkst Canary | 7 | 8 | 7 | 8 | 7 | 7 | 7 | 7.2 |
| Illusive Networks Enterprise | 8 | 7 | 8 | 9 | 8 | 7 | 7 | 7.8 |
| Cymulate Enterprise | 8 | 7 | 8 | 9 | 8 | 7 | 7 | 7.8 |
Interpretation: Scores compare core features, usability, integration, security, performance, and value. Higher weighted totals indicate better overall balance. Organizations should align scoring with priorities, scale, and regulatory needs.
Which Deception Technology Tool Is Right for You?
Solo / Freelancer
- Lightweight solutions like Thinkst Canary provide fast deployment and basic decoys for SMBs.
SMB
- Cymulate Deception or TrapX DeceptionGrid offer scalable deception for mid-market networks.
Mid-Market
- Illusive Networks or Fidelis Deception deliver advanced attack path detection and analytics.
Enterprise
- Enterprises require Attivo ThreatDefend, TrapX DeceptionGrid Enterprise, or Illusive Networks Enterprise for large-scale, hybrid network deployments.
Budget vs Premium
- SMBs can use lightweight deception sensors.
- Premium platforms provide AI-driven detection, automated remediation, and enterprise-scale analytics.
Feature Depth vs Ease of Use
- Advanced solutions like Attivo ThreatDefend provide deep visibility but require SOC expertise.
- Lightweight options balance simplicity with actionable alerts.
Integrations & Scalability
- Enterprise adoption requires SIEM, SOAR, MFA, and hybrid network integrations.
Security & Compliance Needs
- Organizations in regulated industries should ensure SOC 2, ISO 27001, GDPR, and HIPAA compliance support.
Frequently Asked Questions (FAQs)
What pricing models do deception technology tools use?
Most solutions offer subscription-based or enterprise licensing per endpoint, user, or network segment.
Can these tools detect insider threats?
Yes, decoys and behavioral analytics detect anomalous internal activity.
Are deception platforms cloud-native?
Many modern platforms deploy cloud-native decoys for rapid scalability.
Can small businesses benefit from deception technology?
Yes, lightweight decoy solutions are effective for SMBs with minimal infrastructure.
Do these tools integrate with SIEM or SOAR?
Yes, integration allows automated alerts, responses, and forensic reporting.
How quickly can decoys be deployed?
Cloud-native platforms can deploy decoys in hours; enterprise setups may take days.
Do they support cloud and hybrid environments?
Yes, most enterprise tools cover endpoints, on-premises systems, and cloud assets.
Can deception platforms simulate attacks?
Yes, many include attack path simulation to test network and SOC readiness.
Are compliance reports included?
Most tools offer dashboards and reporting templates aligned with regulatory requirements.
Can deception technology reduce dwell time?
Yes, by detecting attacks early and alerting security teams, dwell time is minimized.
Conclusion
Deception Technology Tools provide proactive threat detection, insider threat mitigation, and attacker behavior analysis across enterprise, hybrid, and cloud networks. Small teams can leverage lightweight solutions like Thinkst Canary, mid-market organizations benefit from Cymulate or TrapX, and enterprises require Attivo ThreatDefend or Illusive Networks Enterprise for large-scale deployments. Organizations should shortlist 2–3 solutions, pilot deployment for usability and integration, and ensure compliance and automated alerting to strengthen overall security posture.