Upgrade & Secure Your Future with DevOps, SRE, DevSecOps, MLOps!
We spend hours scrolling social media and waste money on things we forget, but won’t spend 30 minutes a day earning certifications that can change our lives.
Master in DevOps, SRE, DevSecOps & MLOps by DevOps School!
Learn from Guru Rajesh Kumar and double your salary in just one year.
Introduction
Zero Trust Network Access (ZTNA) tools are security solutions that provide secure remote access to applications and services based on strict identity verification and context-aware policies. In plain English, ZTNA assumes that no user, device, or network is inherently trusted, and access is granted only after continuous verification of identity, device posture, and user context. Unlike traditional VPNs, ZTNA ensures granular access control, minimizing the risk of unauthorized access and lateral movement within networks.
In and beyond, ZTNA solutions are critical as organizations embrace hybrid work models, cloud-first strategies, and digital transformation initiatives. Cyber threats are increasingly sophisticated, and perimeter-based security is no longer sufficient. ZTNA helps organizations enforce zero-trust principles, securing remote access, reducing attack surfaces, and improving visibility into user and device behavior.
Real-world use cases include:
- Providing secure remote access to SaaS and on-premises applications for distributed teams.
- Enforcing conditional access policies based on device posture, location, or user behavior.
- Protecting sensitive applications from lateral movement by compromised accounts.
- Integrating with multi-factor authentication (MFA) and identity providers for strong access control.
- Enabling secure cloud adoption while reducing VPN dependency.
Key criteria buyers should evaluate:
- Identity and device verification mechanisms.
- Granular, policy-based access control.
- Cloud, SaaS, and on-premises application support.
- Integration with identity providers (IdPs) and MFA solutions.
- Monitoring, analytics, and reporting capabilities.
- Ease of deployment and scalability for remote workforces.
- Zero-trust enforcement across hybrid networks.
- AI-powered threat detection and behavioral analytics.
- Pricing, licensing flexibility, and multi-tenant support.
Best for: Security teams, IT administrators, and enterprises with hybrid or remote workforce models, cloud-first strategies, and regulated industry requirements.
Not ideal for: Small organizations with minimal remote access needs, where VPN solutions may suffice.
Key Trends in Zero Trust Network Access (ZTNA) Tools
- AI and Behavioral Analytics: Detect anomalous user or device activity for risk-based access decisions.
- Cloud-Native ZTNA Platforms: SaaS delivery reduces infrastructure overhead and scales globally.
- Integration with Identity Providers: Seamless SSO, MFA, and conditional access policies.
- Micro-Segmentation of Applications: Limit lateral movement and enforce least-privilege access.
- Real-Time Monitoring and Logging: Continuous visibility into user activity and device posture.
- Multi-Cloud and Hybrid Deployment Support: Secure access across cloud, on-prem, and hybrid networks.
- Automated Policy Enforcement: Dynamic adjustment of access based on risk scores and user behavior.
- Zero Trust SASE Integration: Combine SWG, CASB, and ZTNA under a unified secure access architecture.
- Adaptive Access Controls: Context-aware policies considering device health, location, and threat intelligence.
- Flexible Licensing Models: Subscription or per-user pricing for SMBs and large enterprises.
How We Selected These Tools (Methodology)
- Evaluated market adoption and recognition among security and IT professionals.
- Assessed feature completeness for identity verification, access control, analytics, and reporting.
- Reviewed reliability and performance metrics such as connection stability and latency.
- Considered integration with MFA, IdPs, SIEM, SWG, and CASB.
- Analyzed security posture including encryption, audit logs, and compliance support.
- Evaluated scalability across global, hybrid, and remote user bases.
- Assessed AI-driven capabilities for risk detection and behavioral analytics.
- Reviewed vendor support, training, and community engagement.
- Balanced enterprise-grade functionality with ease-of-use for smaller deployments.
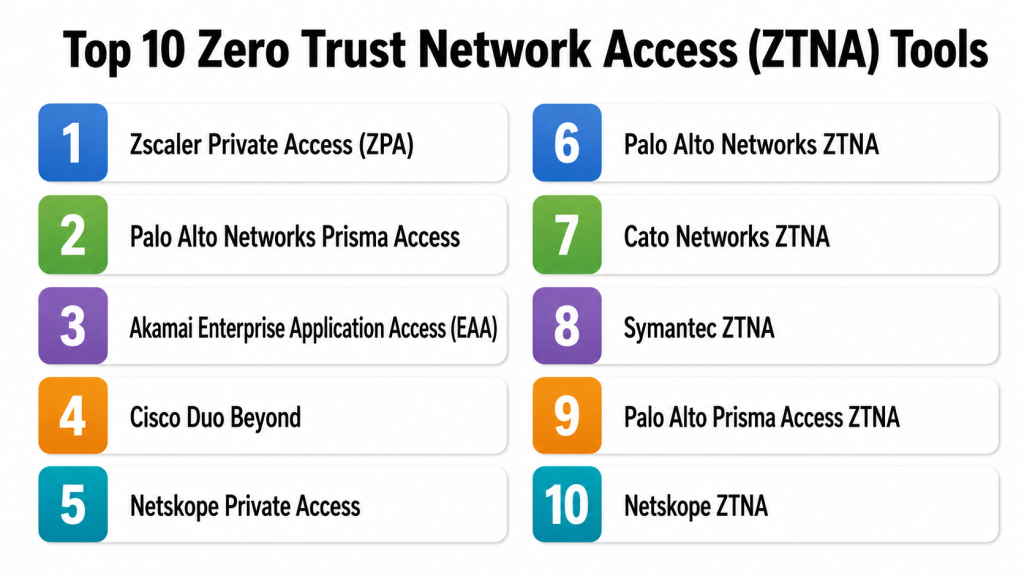
Top 10 Zero Trust Network Access (ZTNA) Tools
#1 — Zscaler Private Access (ZPA)
Short description: ZPA provides cloud-native ZTNA for secure access to internal applications without exposing the network. It is ideal for large enterprises and organizations with distributed remote workforces.
Key Features
- Identity-based access control.
- Application segmentation and micro-segmentation.
- Cloud-native deployment.
- Integration with IdPs and MFA.
- Detailed analytics and reporting.
Pros
- Reduces VPN reliance.
- Strong zero-trust enforcement.
Cons
- Premium pricing.
- Requires planning for enterprise-scale deployment.
Platforms / Deployment
- Web / Cloud.
Security & Compliance
- SSO/MFA, encryption, RBAC.
- SOC 2, ISO 27001, GDPR supported.
Integrations & Ecosystem
- Integrates with Okta, Azure AD, and SIEM systems.
- API access for automation.
- Supports hybrid and cloud applications.
Support & Community
- Vendor support included.
- Extensive documentation and training resources.
#2 — Palo Alto Networks Prisma Access
Short description: Prisma Access delivers ZTNA as part of its SASE platform, securing web and private application access with cloud scalability and zero-trust policies.
Key Features
- Secure access to cloud and on-prem applications.
- Identity-aware access policies.
- SSL inspection and threat protection.
- Integration with multi-factor authentication.
- Analytics and reporting dashboards.
Pros
- Enterprise-grade ZTNA.
- Scales for global remote workforces.
Cons
- Premium pricing.
- Complexity for smaller IT teams.
Platforms / Deployment
- Web / Cloud.
Security & Compliance
- SSO/MFA, encryption.
- SOC 2, ISO 27001, GDPR supported.
Integrations & Ecosystem
- Integrates with IdPs, SIEM, and endpoint security tools.
- API support for automation.
- Supports cloud and hybrid applications.
Support & Community
- Vendor support available.
- Documentation, training, and webinars.
#3 — Akamai Enterprise Application Access (EAA)
Short description: Akamai EAA provides secure, zero-trust access to internal applications without exposing the network. Suitable for global enterprises with hybrid IT environments.
Key Features
- Application-level segmentation.
- Context-aware access policies.
- Cloud-based deployment.
- Integration with SSO and MFA.
- Threat detection and analytics.
Pros
- Strong global reach and low latency.
- Cloud-native with zero-trust enforcement.
Cons
- Enterprise pricing.
- Advanced configurations require expertise.
Platforms / Deployment
- Web / Cloud.
Security & Compliance
- SSO/MFA, encryption.
- ISO 27001, SOC 2 compliance.
Integrations & Ecosystem
- IdP integration (Okta, Azure AD).
- API support for policy automation.
- Works with SaaS and on-prem apps.
Support & Community
- Vendor support included.
- Knowledge base and training.
#4 — Cisco Duo Beyond
Short description: Duo Beyond implements ZTNA principles by enforcing device trust, identity verification, and application-level access for enterprises and SMBs.
Key Features
- Device posture verification.
- Identity-aware access controls.
- MFA integration.
- Application-level segmentation.
- Real-time reporting and analytics.
Pros
- Strong device security integration.
- Simple deployment for SMBs and enterprises.
Cons
- Limited network-level control.
- Enterprise features require higher-tier plans.
Platforms / Deployment
- Web / Cloud.
Security & Compliance
- SSO/MFA, encryption.
- SOC 2, GDPR supported.
Integrations & Ecosystem
- Integrates with IdPs, SIEM, and endpoint management tools.
- API support for automation.
- Supports cloud and on-premises apps.
Support & Community
- Vendor support included.
- Training and knowledge base.
#5 — Netskope Private Access
Short description: Netskope Private Access offers ZTNA with secure application access, traffic visibility, and cloud integration for global enterprises.
Key Features
- Cloud and on-prem app access.
- Identity-aware and risk-based policies.
- SSL/TLS inspection.
- Threat detection and reporting.
- Integration with MFA and IdPs.
Pros
- Scalable cloud-native architecture.
- Strong zero-trust enforcement.
Cons
- Premium pricing.
- Onboarding requires configuration expertise.
Platforms / Deployment
- Web / Cloud.
Security & Compliance
- SSO/MFA, encryption.
- SOC 2, ISO 27001 supported.
Integrations & Ecosystem
- Integrates with IdPs, SIEM, CASB.
- API support for policy automation.
- Works with hybrid apps.
Support & Community
- Vendor support included.
- Documentation and online training.
#6 — Palo Alto Networks ZTNA
Short description: This ZTNA solution secures application access with strict identity verification, policy-based segmentation, and cloud scalability.
Key Features
- Application-level access controls.
- Identity verification and device posture checks.
- Integration with MFA and SSO.
- Cloud-native deployment.
- Analytics and reporting.
Pros
- Enterprise-grade ZTNA.
- Supports cloud and on-premises applications.
Cons
- Premium pricing.
- Advanced configurations require expertise.
Platforms / Deployment
- Web / Cloud.
Security & Compliance
- SSO/MFA, encryption.
- SOC 2, GDPR, ISO 27001.
Integrations & Ecosystem
- SIEM, CASB, IdP integration.
- API support for automation.
- Supports cloud and hybrid applications.
Support & Community
- Vendor support included.
- Training and documentation.
#7 — Cato Networks ZTNA
Short description: Cato Networks delivers ZTNA through its SASE platform, providing secure remote access with cloud scalability and granular access policies.
Key Features
- Cloud-native deployment.
- Identity and device verification.
- Policy-based access control.
- Analytics and reporting dashboards.
- Integration with MFA and IdPs.
Pros
- Fully cloud-native solution.
- Zero-trust enforcement for distributed users.
Cons
- Higher cost for smaller organizations.
- Requires planning for global deployments.
Platforms / Deployment
- Web / Cloud.
Security & Compliance
- SSO/MFA, encryption.
- SOC 2, ISO 27001 supported.
Integrations & Ecosystem
- IdPs, SIEM, and CASB integration.
- API access for policy automation.
- Works with SaaS and on-prem applications.
Support & Community
- Vendor support included.
- Documentation and training.
#8 — Symantec ZTNA
Short description: Symantec ZTNA secures access to applications using identity verification, device posture, and risk-based policies for enterprise and hybrid cloud deployments.
Key Features
- Application-level access control.
- Identity verification and MFA.
- Device posture checking.
- Cloud and on-premises app support.
- Reporting and analytics.
Pros
- Strong enterprise compliance features.
- Flexible cloud and on-prem support.
Cons
- Complexity in deployment for hybrid environments.
- Premium pricing.
Platforms / Deployment
- Web / Cloud / Hybrid.
Security & Compliance
- SSO/MFA, encryption, RBAC.
- SOC 2, ISO 27001, GDPR.
Integrations & Ecosystem
- IdPs, CASB, SIEM integration.
- API access for automation.
- Supports cloud and hybrid apps.
Support & Community
- Vendor support included.
- Documentation and knowledge base.
#9 — Palo Alto Prisma Access ZTNA
Short description: Part of Prisma Access SASE platform, this ZTNA solution provides secure, zero-trust access to all applications with policy enforcement and analytics.
Key Features
- Cloud-based deployment.
- Identity-aware access control.
- Device verification and MFA.
- Analytics and reporting dashboards.
- Policy-based segmentation.
Pros
- Scalable for global enterprise deployments.
- Enterprise-grade security.
Cons
- Premium pricing.
- Complex setup for hybrid environments.
Platforms / Deployment
- Web / Cloud.
Security & Compliance
- SSO/MFA, encryption.
- SOC 2, ISO 27001, GDPR.
Integrations & Ecosystem
- IdPs, SIEM, CASB integration.
- API support for policy automation.
- Cloud and hybrid app support.
Support & Community
- Vendor support included.
- Training and documentation.
#10 — Netskope ZTNA
Short description: Netskope ZTNA provides secure, zero-trust access to applications and cloud services with adaptive policy enforcement and analytics.
Key Features
- Identity and device verification.
- Application segmentation and policy enforcement.
- Cloud-native deployment.
- Real-time analytics and reporting.
- Integration with MFA and IdPs.
Pros
- Scalable cloud-native solution.
- Strong zero-trust enforcement.
Cons
- Enterprise pricing.
- Onboarding requires planning.
Platforms / Deployment
- Web / Cloud.
Security & Compliance
- SSO/MFA, encryption.
- SOC 2, ISO 27001, GDPR.
Integrations & Ecosystem
- IdP, CASB, SIEM integration.
- API support for automation.
- Hybrid and cloud app support.
Support & Community
- Vendor support included.
- Documentation and online training.
Comparison Table (Top 10)
| Tool Name | Best For | Platform(s) Supported | Deployment | Standout Feature | Public Rating |
|---|---|---|---|---|---|
| Zscaler Private Access | Enterprise | Web | Cloud | Cloud-native ZTNA | N/A |
| Prisma Access | Enterprise | Web | Cloud | Distributed application access | N/A |
| Akamai EAA | Enterprise | Web | Cloud | Application-level segmentation | N/A |
| Cisco Duo Beyond | SMB / Enterprise | Web | Cloud | Device posture verification | N/A |
| Netskope Private Access | Enterprise | Web | Cloud | Adaptive policy enforcement | N/A |
| Palo Alto Networks ZTNA | Enterprise | Web | Cloud | Identity-aware access | N/A |
| Cato Networks ZTNA | Enterprise | Web | Cloud | Cloud-native SASE ZTNA | N/A |
| Symantec ZTNA | Enterprise | Web | Cloud / Hybrid | Risk-based policies | N/A |
| Prisma Access ZTNA | Enterprise | Web | Cloud | Cloud-based ZTNA | N/A |
| Netskope ZTNA | Enterprise | Web | Cloud | Adaptive access policies | N/A |
Evaluation & Scoring of ZTNA Tools
| Tool Name | Core (25%) | Ease (15%) | Integrations (15%) | Security (10%) | Performance (10%) | Support (10%) | Value (15%) | Weighted Total (0–10) |
|---|---|---|---|---|---|---|---|---|
| Zscaler Private Access | 9 | 8 | 8 | 9 | 9 | 8 | 7 | 8.4 |
| Prisma Access | 8 | 7 | 8 | 9 | 8 | 7 | 7 | 7.8 |
| Akamai EAA | 8 | 7 | 8 | 9 | 8 | 7 | 7 | 7.8 |
| Cisco Duo Beyond | 7 | 8 | 7 | 8 | 7 | 7 | 7 | 7.4 |
| Netskope Private Access | 8 | 7 | 8 | 9 | 8 | 7 | 7 | 7.8 |
| Palo Alto Networks ZTNA | 8 | 7 | 8 | 9 | 8 | 7 | 7 | 7.8 |
| Cato Networks ZTNA | 8 | 7 | 8 | 9 | 8 | 7 | 7 | 7.8 |
| Symantec ZTNA | 8 | 7 | 7 | 9 | 8 | 7 | 7 | 7.7 |
| Prisma Access ZTNA | 8 | 7 | 8 | 9 | 8 | 7 | 7 | 7.8 |
| Netskope ZTNA | 8 | 7 | 8 | 9 | 8 | 7 | 7 | 7.8 |
Interpretation: Higher scores indicate a more balanced solution across core features, usability, integration, security, and value. Scoring is comparative and should be aligned with organizational priorities.
Which ZTNA Tool Is Right for You?
Solo / Freelancer
- Cloud-native ZTNA like Cisco Duo Beyond provides simple access verification without complex deployments.
SMB
- Netskope Private Access or Cato Networks ZTNA offers scalable, cloud-native access for small and mid-sized teams.
Mid-Market
- Prisma Access, Akamai EAA, or Zscaler Private Access provide robust policy enforcement and analytics.
Enterprise
- Enterprises require Zscaler Private Access, Prisma Access ZTNA, or Symantec ZTNA for global scale, hybrid integration, and compliance support.
Budget vs Premium
- SMBs may use lightweight solutions like Cisco Duo Beyond.
- Enterprises benefit from cloud-native, feature-rich platforms like Zscaler or Prisma Access.
Feature Depth vs Ease of Use
- Deep-feature platforms require onboarding but provide advanced access policies.
- Lightweight solutions balance usability and zero-trust enforcement.
Integrations & Scalability
- Platforms with IdP, CASB, SIEM, and cloud app integrations are essential for mid-market and enterprise scalability.
Security & Compliance Needs
- Regulated industries should prioritize SOC 2, ISO 27001, HIPAA, and GDPR support with continuous access monitoring.
Frequently Asked Questions (FAQs)
What pricing models do ZTNA tools use?
Pricing ranges from subscription-based SaaS to enterprise licensing per user, device, or application.
Can ZTNA tools replace VPNs?
Yes, ZTNA provides secure, identity-aware access without exposing the network like traditional VPNs.
Are ZTNA solutions cloud-native?
Most modern ZTNA solutions are SaaS-based for global scalability and reduced infrastructure overhead.
Do these tools integrate with MFA and IdPs?
Yes, integration with identity providers and multi-factor authentication is standard for ZTNA.
Can ZTNA enforce conditional access policies?
Yes, access is granted based on device posture, user context, location, and risk scores.
Are compliance reports included?
Most enterprise ZTNA platforms offer dashboards and templates for regulatory compliance.
Can small businesses benefit from ZTNA?
Yes, lightweight cloud-native ZTNA solutions support SMBs with remote or hybrid teams.
Do these tools monitor application usage?
Yes, ZTNA platforms track access to applications and enforce least-privilege policies.
Can ZTNA prevent lateral movement inside the network?
Yes, micro-segmentation and application-level access control reduce lateral movement risks.
Are ZTNA tools compatible with multi-cloud environments?
Yes, leading solutions support AWS, Azure, Google Cloud, and hybrid deployments.
Conclusion
Zero Trust Network Access (ZTNA) tools are critical for securing application access in modern hybrid and cloud-first enterprises. Selecting the right ZTNA depends on workforce distribution, cloud adoption, and compliance requirements. SMBs may leverage Cisco Duo Beyond or Netskope Private Access, mid-market organizations benefit from Prisma Access or Akamai EAA, while enterprises require robust solutions like Zscaler Private Access or Symantec ZTNA. Organizations should shortlist 2–3 platforms, conduct a pilot to validate ease-of-use and integrations, and confirm compliance and zero-trust enforcement before full deployment.