Upgrade & Secure Your Future with DevOps, SRE, DevSecOps, MLOps!
We spend hours scrolling social media and waste money on things we forget, but won’t spend 30 minutes a day earning certifications that can change our lives.
Master in DevOps, SRE, DevSecOps & MLOps by DevOps School!
Learn from Guru Rajesh Kumar and double your salary in just one year.
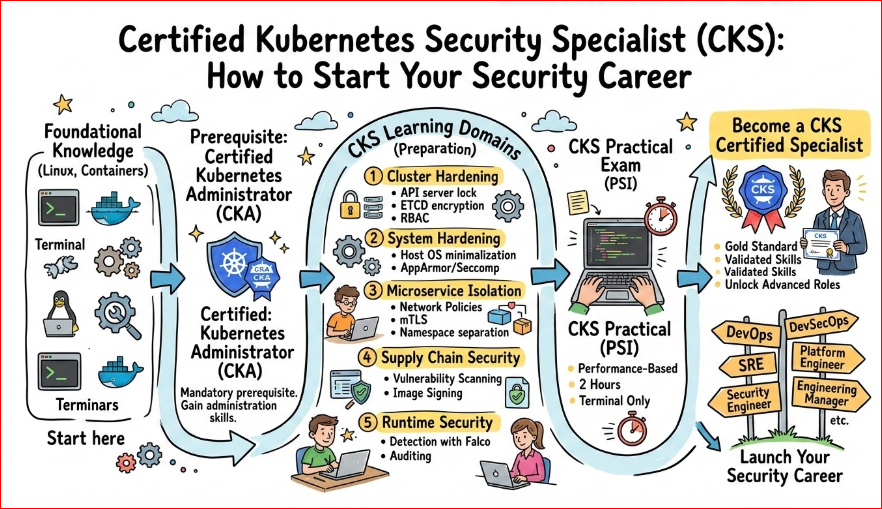
The modern world runs on the cloud, and the cloud runs on Kubernetes. As more companies move their critical workloads to containers, the risks increase. It is no longer enough to just know how to run a cluster; you must know how to lock it down effectively. Securing a Kubernetes environment is a journey that starts from the moment you write your first line of code and continues long after your application is live. The Certified Kubernetes Security Specialist (CKS) program is designed to give you the skills needed to protect every layer of this complex stack.
Understanding the Kubernetes Certification Landscape
Before diving deep into security, it is important to see where CKS fits in the bigger picture of Cloud Native expertise. Kubernetes certifications are structured to take you from a beginner to a specialized expert in a logical progression. The landscape starts with basic literacy and moves into administration and development before reaching advanced security specialization. By following this path, you ensure that you have the foundational knowledge of how clusters work before you attempt to secure them against advanced threats.
| Track | Level | Who it’s for | Prerequisites | Skills Covered | Recommended Order |
| Security | Advanced | Security Engineers, DevOps, SREs | CKA Certification | Cluster hardening, System hardening, Supply chain security | 3rd (After CKA) |
| Administration | Intermediate | System Admins, Cloud Engineers | None | Installation, Configuration, Troubleshooting | 2nd (After KCNA) |
| Development | Intermediate | Software Developers | None | Application resources, Observability, Security | 2nd (After KCNA) |
| Foundational | Entry | Managers, Students, Beginners | None | Basic Cloud Native concepts | 1st |
Detailed Breakdown: Certified Kubernetes Security Specialist (CKS)
What it is
The CKS is a performance-based certification that tests your ability to secure container-based applications and Kubernetes platforms during build, deployment, and runtime. It is not a theoretical exam but a practical test where you solve real security problems in a live command-line environment. This ensures that a certified professional can actually do the work rather than just memorizing facts. It is widely considered one of the most elite certifications in the entire Cloud Native ecosystem.
Who should take it
This certification is ideal for experienced DevOps engineers, Security professionals, and Site Reliability Engineers (SREs) who manage production clusters. If you are responsible for maintaining the integrity of data and ensuring that your applications are safe from hackers, this is for you. It is also highly beneficial for Cloud Architects who need to design secure infrastructure from the ground up.
Skills you’ll gain
- Cluster Setup: You will learn how to secure the API server, restrict access to the metadata API, and manage administrative certificates properly.
- System Hardening: This involves reducing the attack surface of the host OS, using tools like AppArmor and Seccomp to limit what processes can do.
- Minimize Microservice Vulnerabilities: You will master Pod Security Standards and Network Policies to ensure that if one pod is compromised, the rest stay safe.
- Supply Chain Security: You will learn to scan images for vulnerabilities, sign your metadata, and ensure only trusted code runs in your cluster.
- Monitoring & Logging: You will gain the ability to detect threats at runtime using tools like Falco and perform deep security audits of your cluster activities.
Real-world projects you should be able to do
- Build a private container registry that automatically blocks any image with “High” or “Critical” vulnerabilities from being deployed.
- Implement a “Zero Trust” network architecture where every microservice must prove its identity and is only allowed to talk to specific partners.
- Configure an automated runtime security system that alerts the security team the moment a bash shell is opened inside a production pod.
- Conduct a full audit of an existing cluster to identify and fix misconfigured RBAC settings that give too much power to standard users.
Preparation Plan
- 7–14 days: This fast-track is best for those already managing security in production environments. Focus on the specific exam environment, practicing the official curriculum, and getting comfortable with the time limits.
- 30 days: This is the ideal timeframe for active CKA holders who use Kubernetes daily. Spend an hour each day practicing Falco, AppArmor, and Network Policy syntax until it becomes second nature.
- 60 days: Recommended for engineers who are strong in DevOps but new to the security mindset. Spend the first month learning Linux security basics and kernel features before diving into the specific Kubernetes security tools.
Common Mistakes
- Ignoring the CKA basics: You must be incredibly fast at basic
kubectlcommands. If you spend too much time looking up how to create a pod, you will run out of time for the security tasks. - Forgetting Context: The exam uses multiple clusters. A very common mistake is applying a perfect security fix to the wrong cluster because you forgot to switch contexts.
- Typos in YAML: A single misplaced space in a Network Policy or Pod Security admission controller can break your entire configuration. Practice writing clean YAML manually without relying on auto-completion.
- Not using the documentation: The official Kubernetes documentation is your only resource during the exam. You must learn exactly where the security examples are located so you can find them in seconds.
Best next certification after this
Once you master Kubernetes security, the logical next step is exploring Cloud-specific security certifications like the AWS or Azure Security Specialty. You might also move into DevSecOps automation to learn how to integrate these checks into a full CI/CD pipeline. For those looking at a broader view, a Cloud Security Professional (CCSP) certificate provides a great high-level overview of global security standards.
Choose Your Path: Learning Tracks
- DevOps Path: This track focuses on the “Speed of Delivery” while ensuring the infrastructure is stable. You learn how to automate the deployment of secure infrastructure so that security is a built-in feature of the pipeline, not a bottleneck.
- DevSecOps Path: This is the direct home for CKS and focuses on the “Shift Left” philosophy. The goal is to put security checks at the very start of the development process, catching bugs before they ever reach the production cluster.
- SRE Path: This path focuses on “Reliability” and system uptime. You use security tools to ensure that system failures aren’t caused by malicious actors, and you use observability to detect when a security breach is impacting performance.
- AIOps/MLOps Path: This track is about securing the massive data pipelines and model training environments that run on Kubernetes. It ensures that the sensitive data used to train AI models is protected from unauthorized access or theft.
- DataOps Path: This path concentrates on data encryption, access control, and compliance with privacy laws like GDPR within containerized databases. It is essential for anyone managing stateful applications and sensitive user information in the cloud.
- FinOps Path: While mostly about cost management, security plays a major role here. This track helps you ensure that “shadow IT” or unauthorized clusters aren’t inflating the bill and that cost-saving measures don’t create new security gaps.
Role → Recommended Certifications Mapping
| Role | Level | Core Certification | Specialized Certification | Advanced/Leadership Step |
| DevOps Engineer | Professional | CKA (Administrator) | CKS (Security) | Terraform Associate / GitOps |
| SRE | Professional | CKA (Administrator) | PCA (Prometheus) | CKS (Security) |
| Platform Engineer | Professional | CKA (Administrator) | CKS (Security) | Certified GitOps Associate |
| Cloud Engineer | Professional | Cloud Provider Associate (AWS/Azure) | CKA (Administrator) | CKS (Security) |
| Security Engineer | Specialist | CKS (Security) | CKA (Administrator) | CCSP (Cloud Security) |
| Data Engineer | Specialist | CKA (Administrator) | CKS (Security) | Databricks / Snowflake Certs |
| FinOps Practitioner | Specialist | FinOps Certified Practitioner | KCNA (Foundational) | CKA (Administrator) |
| Engineering Manager | Management | KCNA (Foundational) | CKA (Administrator) | CISM (Security Manager) |
Top Institutions for CKS Training
- DevOpsSchool: This institution offers comprehensive, instructor-led training that focuses heavily on real-world labs. Their instructors are industry veterans who provide specific strategies for passing the CKS exam on your first try.
- Cotocus: Known for their very practical, hands-on approach, Cotocus dives deep into the fundamentals of container orchestration. They ensure you understand the “why” behind security, not just the “how” of the commands.
- Scmgalaxy: This platform provides a massive library of community resources and structured bootcamps. It is a great place to find deep-dive articles and community support for various DevOps and security tools.
- BestDevOps: They focus on high-quality video content and practice exams that are designed to simulate the actual CKS environment. Their materials are updated frequently to match the latest Kubernetes versions and exam patterns.
- devsecopsschool.com: As the name suggests, this is a specialized platform for security-first engineering. It is the perfect choice for professionals who want to transition from traditional DevOps into a specialized DevSecOps career.
- sreschool.com: This institution tailors its training toward the intersection of reliability and security. They teach you how security misconfigurations can lead to system downtime and how to prevent those issues through better engineering.
- aiopsschool.com: This school bridges the gap between artificial intelligence operations and secure infrastructure. It is ideal for those working on modern AI stacks that require high-performance, secure Kubernetes clusters.
- dataopsschool.com: They focus specifically on the security and management of data-heavy workloads. Their training covers how to handle persistent storage and database security within a Kubernetes environment effectively.
- finopsschool.com: This platform provides the unique context of managing cloud security costs. They teach you how to maintain a high-security posture without overspending on unnecessary cloud resources or inefficient configurations.
Frequently Asked Questions (FAQs)
General Kubernetes & Career FAQs
- How hard is the CKS compared to CKA? It is significantly more difficult because it requires a deeper understanding of the Linux kernel and external security tools. While CKA tests if you can build a house, CKS tests if you can protect it against professional intruders.
- How much time should I dedicate to study? If you are working a full-time job, you should plan for at least 4 to 6 weeks of daily study. Consistency is more important than long hours, so try to spend at least 60 minutes every day.
- Does CKS help in getting a salary hike? Yes, security is currently a premium skill in the tech market. Engineers with the CKS certification often see a 20-30% increase in their market value compared to those with just basic certifications.
- Can I take CKS without CKA? No, you cannot. The CKA is a mandatory prerequisite, and you must have a valid, active CKA certification before you are even allowed to sit for the CKS exam.
- What is the validity of the CKS certificate? The CKS certification is currently valid for 2 years. Because technology in the cloud-native space moves so fast, the Linux Foundation requires you to recertify to prove your skills are still current.
- Is the exam multiple-choice? No, it is a 100% performance-based exam. You are given a terminal and a series of real-world scenarios that you must solve by configuring live Kubernetes clusters within a time limit.
- What happens if I fail the first attempt? Most official exam vouchers from the Linux Foundation include one free retake. You should use your first attempt to understand the exam’s pacing and identify your weakest technical areas.
- Is CKS relevant for managers? Absolutely. It helps managers understand the real risks associated with containerized workloads. It also gives them the knowledge needed to advocate for the right security tools and resources for their teams.
- Which cloud provider is used in the exam? The exam is cloud-agnostic, meaning it uses standard Kubernetes distributions. The skills you learn will apply whether you are using AWS EKS, Google GKE, Azure AKS, or on-premise clusters.
- Do I need to know programming? You do not need to be a software developer, but you should be comfortable with Shell scripting. You will also need to be able to read and understand basic configuration files written in YAML and JSON.
- Will this help me move into a Security Engineer role? Yes, it is one of the most respected “hands-on” certifications in the industry. It proves to employers that you can handle the specific security challenges of modern, containerized infrastructure.
- Is it worth it right now? As long as companies continue to move their business to the cloud, security will remain their top priority. This certification is a future-proof investment in a high-demand career path.
Frequently Asked Questions (FAQs) About the CKS Certification
1. Is the CKS exam more difficult than the CKA? Yes, significantly. While the CKA focuses on making the cluster functional, the CKS focuses on making it “hostile” to intruders. It requires a much deeper understanding of the Linux kernel, system calls, and third-party security tools like Falco and Trivy. You aren’t just managing resources; you are auditing them for tiny, dangerous flaws.
2. How long should I realistically study if I already have my CKA? If you are working with Kubernetes daily, a dedicated window of 4 to 6 weeks is usually sufficient. You need enough time to move beyond just reading documentation to building “muscle memory” for the command line. Consistency—spending at least one hour every evening—is far more effective than trying to cram for 10 hours on a weekend.
3. Do I need to be a security professional to pass this? Not at all. This certification is designed for “builders” who want to become “secure builders.” While a background in security helps with the mindset, the exam is purely technical and administrative. If you understand how Kubernetes works, you can learn the specific steps required to lock it down.
4. What is the most common reason people fail the CKS on their first try? Time management is the biggest hurdle. The exam is only 120 minutes long, and the tasks are complex. Many candidates spend too much time on a single difficult problem instead of moving on to easier points. Also, forgetting to switch “contexts” (clusters) before running a command is a very common mistake that leads to lost marks.
5. How much of the exam is based on third-party tools versus native Kubernetes? About 30-40% of the exam involves tools that are not part of the standard Kubernetes binary, such as Falco for runtime security, Trivy for image scanning, and AppArmor for Linux hardening. You must be comfortable installing, configuring, and reading the logs of these specific tools to succeed.
6. Can I use a “cheat sheet” during the performance-based exam? No personal notes or physical cheat sheets are allowed. However, you are permitted to open one additional browser tab to access official documentation sites like the Kubernetes docs and the specific project pages for tools like Falco. Mastering the “search” function of these sites is a critical part of your preparation.
7. Does the CKS cover cloud-specific security like AWS IAM or Azure AD? No, the CKS is strictly cloud-agnostic. It focuses on the security of the Kubernetes platform itself and the underlying Linux nodes. While these skills are vital when working on AWS EKS or Google GKE, the exam stays focused on the open-source components that work everywhere.
8. Is it worth renewing the CKS every two years? Absolutely. The security landscape changes faster than any other area of technology. Vulnerabilities that didn’t exist two years ago are now major threats. Recertifying ensures that your skills remain sharp and that you are still using the current industry best practices to protect your company’s data.
Testimonials
“I had been working in DevOps for years and thought our clusters were safe. The CKS training opened my eyes to the vulnerabilities I was leaving wide open every day. The hands-on labs were the best part of the whole experience.” — Arjun
“Moving from traditional network security to Cloud Native was a huge challenge. CKS gave me a very structured path to understand how containers actually work and how to fix them when things go wrong. It changed my career trajectory.” — Sarah
“As an Engineering Manager, I took the CKS training not to code every day, but to better lead my security team. Now I know exactly what questions to ask during our architecture reviews to ensure we are protected.” — Michael
Conclusion
The journey to becoming a Certified Kubernetes Security Specialist is a challenging one, but it is undoubtedly one of the most rewarding paths in modern IT. It moves you from being someone who simply “deploys code” to being a trusted professional who “protects the business.” Whether you are an engineer in India or working for a global firm, the security skills you gain through CKS are universal and highly valued. Start with the basics, practice in your lab every single day, and don’t be afraid to break things—that is exactly how the best experts are made.