Upgrade & Secure Your Future with DevOps, SRE, DevSecOps, MLOps!
We spend hours scrolling social media and waste money on things we forget, but won’t spend 30 minutes a day earning certifications that can change our lives.
Master in DevOps, SRE, DevSecOps & MLOps by DevOps School!
Learn from Guru Rajesh Kumar and double your salary in just one year.
Introduction
GRC (Data Encryption Tools) are specialized solutions that help organizations secure sensitive data through encryption, tokenization, and key management. In simple terms, these tools protect confidential information—whether in transit, at rest, or in use—from unauthorized access or breaches. They are essential for safeguarding personal data, financial records, intellectual property, and any regulated information.
As cybersecurity threats grow in complexity and regulatory requirements tighten, the importance of data encryption in and beyond cannot be overstated. Organizations must ensure data privacy, mitigate risk, and maintain compliance with standards such as GDPR, HIPAA, and PCI DSS. Modern encryption platforms often include AI-assisted key management, automated compliance reporting, and seamless integration with cloud and on-premises systems.
Real-world use cases include:
- Encrypting sensitive customer data in databases and applications.
- Protecting files stored in cloud environments and SaaS platforms.
- Managing cryptographic keys securely across distributed systems.
- Complying with regulatory frameworks such as GDPR, HIPAA, or PCI DSS.
- Enabling secure file sharing and email communication.
Key criteria buyers should evaluate:
- Encryption strength and algorithm support.
- Key management capabilities and lifecycle management.
- Cloud and on-premises deployment flexibility.
- Compliance with security standards (SOC 2, ISO 27001, GDPR).
- Performance and latency impact.
- Integration with existing IT and security systems.
- AI-assisted analytics and automated reporting.
- Scalability for enterprise workloads.
- User access and role-based security management.
Best for: IT security teams, data protection officers, enterprises in regulated industries, and cloud-native organizations.
Not ideal for: Small companies with minimal sensitive data, or those relying on basic OS-level encryption.
Key Trends in Data Encryption Tools
- AI-Powered Key Management: AI predicts key rotation needs and potential risks.
- Seamless Cloud Integration: Encryption solutions that natively work with public cloud services.
- Automated Compliance Reporting: Platforms generate audit-ready logs automatically.
- End-to-End Encryption for SaaS Applications: Secure data flow between users and cloud apps.
- Quantum-Resistant Algorithms: Preparing for next-generation cryptographic threats.
- Zero-Trust Security Integration: Encryption combined with access controls for secure data use.
- Tokenization for Sensitive Fields: Protecting specific PII and financial data in databases.
- Centralized Dashboard for Key & Policy Management: Unified view of encryption status.
- Cross-Platform Support: Encrypt data across Windows, Linux, macOS, and mobile.
- Flexible Licensing & Deployment Models: SaaS, on-premises, hybrid options for enterprises.
How We Selected These Tools (Methodology)
- Evaluated market adoption and industry recognition.
- Assessed encryption strength, algorithm diversity, and key management.
- Reviewed compliance coverage for HIPAA, GDPR, PCI DSS, and other standards.
- Examined performance and impact on system latency.
- Analyzed integration capabilities with enterprise systems and cloud services.
- Evaluated scalability for enterprise and multi-cloud deployments.
- Assessed AI-assisted analytics, reporting, and automation features.
- Reviewed security posture including SSO, MFA, audit logs, and RBAC.
- Considered vendor support, training, and community resources.
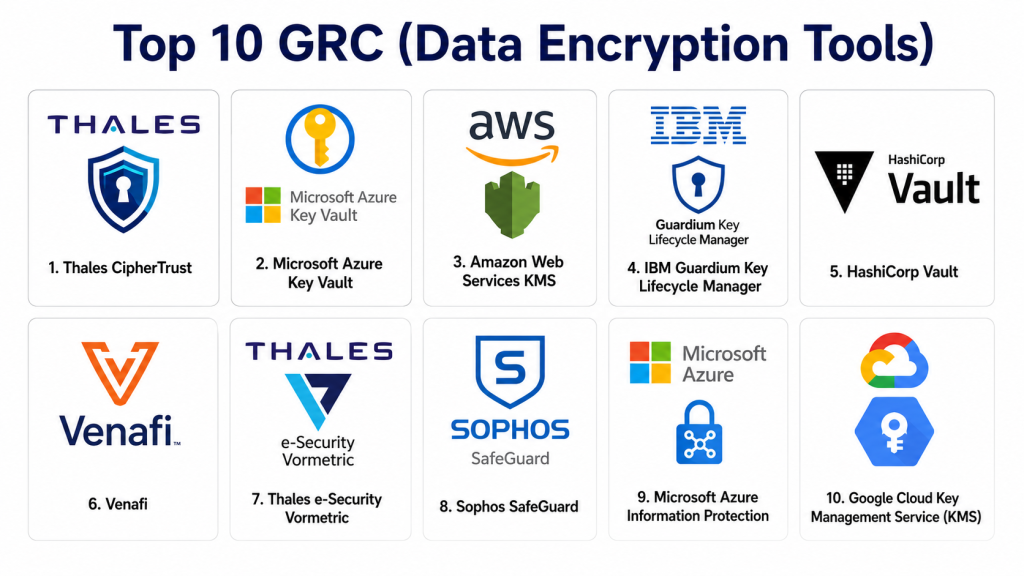
Top 10 GRC (Data Encryption Tools)
#1 — Thales CipherTrust
Short description: Thales CipherTrust provides enterprise-grade encryption, key management, and data security solutions, designed for global organizations with complex compliance needs.
Key Features
- Centralized key management.
- Data discovery and classification.
- Cloud and on-prem encryption.
- Tokenization and masking.
- Audit and compliance reporting.
Pros
- Enterprise-ready with robust compliance support.
- Scalable for multi-cloud environments.
Cons
- Premium pricing for smaller organizations.
- Deployment may require IT support.
Platforms / Deployment
- Web / Windows / Linux / macOS / Cloud / Hybrid.
Security & Compliance
- SOC 2, ISO 27001, GDPR, HIPAA.
- SSO, MFA, RBAC, encryption.
Integrations & Ecosystem
- Cloud platforms (AWS, Azure, GCP).
- Databases and ERP systems.
- API-driven automation.
Support & Community
- Extensive vendor support and training resources.
- Active enterprise user community.
#2 — Microsoft Azure Key Vault
Short description: Azure Key Vault allows organizations to encrypt keys and secrets in the cloud, offering integrated management and policy enforcement for sensitive data.
Key Features
- Key lifecycle management.
- Secret storage and encryption.
- Hardware Security Module (HSM) integration.
- Audit logging and compliance tracking.
- API and SDK support.
Pros
- Deep integration with Azure cloud ecosystem.
- Highly scalable and reliable.
Cons
- Limited to Azure-centric workloads.
- Advanced features may require expertise.
Platforms / Deployment
- Web / Cloud (Azure).
Security & Compliance
- SOC 2, ISO 27001, GDPR.
- SSO, MFA, audit logs.
Integrations & Ecosystem
- Azure services (SQL, Storage, VMs).
- CI/CD pipelines and APIs.
- Azure Active Directory integration.
Support & Community
- Vendor support via Microsoft.
- Documentation and active developer forums.
#3 — Amazon Web Services KMS
Short description: AWS KMS provides secure key storage, management, and encryption for workloads running in AWS cloud, enabling automated compliance and centralized key control.
Key Features
- Envelope encryption.
- Automated key rotation.
- IAM-based access control.
- Audit logging with CloudTrail.
- Multi-region replication.
Pros
- Native integration with AWS services.
- Automated compliance and scalability.
Cons
- Limited to AWS ecosystem.
- Learning curve for key policies.
Platforms / Deployment
- Web / Cloud (AWS).
Security & Compliance
- SOC 2, ISO 27001, GDPR, HIPAA.
- MFA, RBAC, encryption.
Integrations & Ecosystem
- AWS services (S3, RDS, Lambda).
- API and SDK access.
- Cloud monitoring integration.
Support & Community
- AWS support plans.
- Extensive community and documentation.
#4 — IBM Guardium Key Lifecycle Manager
Short description: IBM Guardium provides data encryption, key lifecycle management, and centralized compliance reporting for enterprise IT environments.
Key Features
- Key creation and rotation.
- Encryption across databases and applications.
- Policy enforcement and auditing.
- HSM integration.
- Compliance dashboards.
Pros
- Comprehensive enterprise coverage.
- Strong regulatory compliance focus.
Cons
- Higher cost for smaller organizations.
- Complex deployment for SMBs.
Platforms / Deployment
- Web / Windows / Linux / Cloud / Hybrid.
Security & Compliance
- SOC 2, ISO 27001, GDPR, HIPAA.
- MFA, audit logs, RBAC.
Integrations & Ecosystem
- ERP, databases, cloud services.
- API support for automation.
- HSM and SIEM integration.
Support & Community
- IBM enterprise support and training.
- Documentation and forums.
#5 — HashiCorp Vault
Short description: Vault secures secrets, encryption keys, and credentials across dynamic infrastructure, designed for DevOps and cloud-native environments.
Key Features
- Secret and key management.
- Dynamic secrets generation.
- Policy-based access control.
- API-driven automation.
- Multi-cloud support.
Pros
- Ideal for DevOps and cloud-native workflows.
- Open-source flexibility with enterprise features.
Cons
- Self-hosted setup requires DevOps expertise.
- Enterprise features at premium pricing.
Platforms / Deployment
- Web / Windows / Linux / macOS / Cloud / Hybrid.
Security & Compliance
- SOC 2, ISO 27001, GDPR.
- MFA, RBAC, audit logging.
Integrations & Ecosystem
- Cloud providers (AWS, Azure, GCP).
- CI/CD pipelines and infrastructure as code.
- API integration.
Support & Community
- Enterprise support available.
- Active open-source community.
#6 — Venafi
Short description: Venafi focuses on encryption key management and certificate lifecycle management to secure enterprise communications and compliance.
Key Features
- Certificate lifecycle management.
- Key rotation automation.
- Policy enforcement.
- Compliance reporting.
- HSM integration.
Pros
- Excellent certificate and key governance.
- Enterprise-grade compliance features.
Cons
- Complex deployment.
- Premium pricing.
Platforms / Deployment
- Web / Cloud / Hybrid.
Security & Compliance
- SOC 2, ISO 27001, GDPR.
- MFA, RBAC, encryption.
Integrations & Ecosystem
- PKI systems, cloud providers.
- API-driven workflows.
- Security monitoring integrations.
Support & Community
- Vendor support and training.
- Documentation and professional services.
#7 — Thales e-Security Vormetric
Short description: Vormetric provides transparent encryption, tokenization, and key management for enterprise data protection across databases, applications, and cloud services.
Key Features
- Transparent data encryption.
- Tokenization and masking.
- Centralized key management.
- Cloud and on-premises support.
- Audit and compliance reporting.
Pros
- Strong enterprise-grade security.
- Multi-environment support.
Cons
- Higher cost for SMBs.
- Configuration requires expertise.
Platforms / Deployment
- Web / Windows / Linux / Cloud / Hybrid.
Security & Compliance
- SOC 2, ISO 27001, GDPR, HIPAA.
- MFA, audit logs, RBAC.
Integrations & Ecosystem
- Databases, applications, cloud platforms.
- API and automation integration.
- SIEM and analytics support.
Support & Community
- Vendor support and training.
- Documentation and community resources.
#8 — Sophos SafeGuard
Short description: Sophos SafeGuard offers endpoint encryption and central key management, ensuring data security across desktops, laptops, and mobile devices.
Key Features
- Full-disk and file encryption.
- Key management across devices.
- Cloud and on-premises deployment.
- Policy enforcement and compliance tracking.
- Reporting dashboards.
Pros
- User-friendly endpoint encryption.
- Centralized management.
Cons
- Primarily endpoint-focused.
- Limited cloud-native analytics.
Platforms / Deployment
- Windows / macOS / Linux / Cloud.
Security & Compliance
- SOC 2, ISO 27001, GDPR.
- Encryption, MFA, audit logs.
Integrations & Ecosystem
- Endpoint management systems.
- Cloud storage and SaaS integrations.
- API for reporting.
Support & Community
- Vendor support, documentation, and training.
#9 — Microsoft Azure Information Protection
Short description: Azure Information Protection secures documents and emails through encryption and access policies, designed for Microsoft-centric enterprises.
Key Features
- Document and email encryption.
- Policy-based access control.
- Integration with Microsoft 365.
- Audit and reporting dashboards.
- Automated classification and labeling.
Pros
- Seamless integration with Microsoft ecosystem.
- Automated policy enforcement.
Cons
- Limited outside Microsoft environments.
- Licensing may be complex.
Platforms / Deployment
- Windows / Cloud / Mobile.
Security & Compliance
- SOC 2, ISO 27001, GDPR, HIPAA.
- MFA, RBAC, encryption.
Integrations & Ecosystem
- Microsoft 365, Exchange, SharePoint.
- APIs for automated workflows.
- Cloud storage integration.
Support & Community
- Microsoft support and documentation.
- Community and forums.
#10 — Google Cloud Key Management Service (KMS)
Short description: Google Cloud KMS allows secure key storage and management for applications and services in Google Cloud, ensuring encryption and compliance.
Key Features
- Centralized key management.
- HSM-backed security.
- Role-based access control.
- Automated key rotation.
- Audit logging.
Pros
- Native Google Cloud integration.
- Highly scalable for cloud applications.
Cons
- Limited to Google Cloud workloads.
- Advanced features require expertise.
Platforms / Deployment
- Web / Cloud / API.
Security & Compliance
- SOC 2, ISO 27001, GDPR.
- MFA, RBAC, encryption.
Integrations & Ecosystem
- Google Cloud services (Storage, Compute, BigQuery).
- API and SDK integration.
- Security and compliance monitoring.
Support & Community
- Vendor support, documentation, and training.
Comparison Table (Top 10)
| Tool Name | Best For | Platform(s) Supported | Deployment | Standout Feature | Public Rating |
|---|---|---|---|---|---|
| Thales CipherTrust | Enterprise | Web / Windows / Linux / Cloud | Cloud / Hybrid | Centralized key management | N/A |
| Azure Key Vault | Azure Workloads | Web / Cloud | Cloud | Native Azure integration | N/A |
| AWS KMS | AWS Workloads | Web / Cloud | Cloud | Envelope encryption & multi-region | N/A |
| IBM Guardium KLM | Enterprise | Web / Windows / Linux / Cloud | Cloud / Hybrid | Key lifecycle management | N/A |
| HashiCorp Vault | DevOps / Cloud | Web / Windows / Linux / Cloud | Cloud / Hybrid | Secrets & key management | N/A |
| Venafi | Enterprise PKI | Web / Cloud / Hybrid | Cloud / Hybrid | Certificate lifecycle management | N/A |
| Vormetric | Enterprise | Web / Windows / Linux / Cloud | Cloud / Hybrid | Transparent encryption | N/A |
| Sophos SafeGuard | Endpoint Security | Windows / macOS / Linux / Cloud | Cloud / Hybrid | Endpoint encryption | N/A |
| Azure Information Protection | Microsoft 365 | Windows / Cloud / Mobile | Cloud | Document & email encryption | N/A |
| Google Cloud KMS | Google Cloud | Web / Cloud / API | Cloud | Secure key management | N/A |
Evaluation & Scoring of Data Encryption Tools
| Tool Name | Core (25%) | Ease (15%) | Integrations (15%) | Security (10%) | Performance (10%) | Support (10%) | Value (15%) | Weighted Total |
|---|---|---|---|---|---|---|---|---|
| Thales CipherTrust | 9 | 8 | 9 | 9 | 9 | 8 | 7 | 8.4 |
| Azure Key Vault | 9 | 8 | 8 | 9 | 8 | 8 | 7 | 8.1 |
| AWS KMS | 9 | 8 | 8 | 9 | 8 | 8 | 7 | 8.1 |
| IBM Guardium KLM | 8 | 7 | 8 | 9 | 8 | 7 | 7 | 7.8 |
| HashiCorp Vault | 8 | 8 | 8 | 9 | 8 | 7 | 7 | 7.9 |
| Venafi | 8 | 7 | 8 | 9 | 8 | 7 | 7 | 7.8 |
| Vormetric | 9 | 8 | 8 | 9 | 8 | 7 | 7 | 8.0 |
| Sophos SafeGuard | 8 | 8 | 7 | 9 | 8 | 7 | 7 | 7.8 |
| Azure Information Protection | 8 | 8 | 7 | 9 | 8 | 7 | 7 | 7.8 |
| Google Cloud KMS | 8 | 8 | 8 | 9 | 8 | 7 | 7 | 7.9 |
Interpretation: Scores provide a comparative view of encryption strength, ease of deployment, integration capabilities, security compliance, and value. Organizations should prioritize tools based on deployment environment, regulatory requirements, and workload types.
Which Data Encryption Tool Is Right for You?
Solo / Freelancer
- Lightweight cloud-native solutions like Google Cloud KMS or Azure Key Vault for single-project or small business use.
SMB
- HashiCorp Vault or Sophos SafeGuard provides manageable encryption with centralized key management for growing companies.
Mid-Market
- Thales CipherTrust, Vormetric, or IBM Guardium KLM for enterprise-grade encryption and compliance reporting.
Enterprise
- Large-scale deployments require Venafi, Thales CipherTrust, or HashiCorp Vault Enterprise for multi-cloud, multi-region, and advanced key lifecycle management.
Budget vs Premium
- SMBs benefit from SaaS models with essential features.
- Enterprises require full-feature suites with AI, HSM integration, and compliance analytics.
Feature Depth vs Ease of Use
- Enterprise platforms provide deep functionality with configuration effort.
- Smaller deployments prioritize simplicity while covering essential encryption needs.
Integrations & Scalability
- Critical for integrating with cloud providers, on-prem systems, DevOps pipelines, and SaaS applications.
Security & Compliance Needs
- Enterprises in regulated sectors should ensure SOC 2, ISO 27001, GDPR, and HIPAA compliance.
Frequently Asked Questions (FAQs)
What encryption algorithms are supported?
Most enterprise tools support AES, RSA, and elliptic curve algorithms.
Can these tools manage keys across multiple clouds?
Yes, cloud-native and hybrid platforms provide multi-cloud key management.
Are these platforms suitable for SMBs?
Yes, lighter SaaS options like Azure Key Vault or Google Cloud KMS fit SMB requirements.
Do these tools support automated key rotation?
Yes, key rotation can be automated to comply with security policies.
Can encryption impact system performance?
Minimal impact with modern encryption; high-volume workloads may require tuning.
Are these tools compliant with GDPR and HIPAA?
Yes, most enterprise-grade tools maintain compliance with global data regulations.
Can these platforms integrate with DevOps pipelines?
Yes, API and CI/CD integrations are available.
How is audit logging handled?
Platforms provide detailed audit logs for key management and encryption operations.
Are endpoints covered by these solutions?
Some tools, like Sophos SafeGuard, provide endpoint encryption alongside key management.
Do these tools support tokenization and masking?
Yes, advanced platforms support tokenization to protect sensitive data in databases and applications.
Conclusion
GRC Data Encryption Tools are critical for protecting sensitive information, ensuring regulatory compliance, and supporting secure digital operations. SMBs can leverage Google Cloud KMS and Azure Key Vault for cloud-native simplicity, mid-market organizations benefit from HashiCorp Vault and Sophos SafeGuard, while enterprises require Thales CipherTrust, Venafi, and IBM Guardium KLM for advanced key lifecycle management and multi-cloud deployment. Organizations should shortlist 2–3 tools, pilot encryption workflows, and validate integration with existing IT systems to maximize data