Upgrade & Secure Your Future with DevOps, SRE, DevSecOps, MLOps!
We spend hours scrolling social media and waste money on things we forget, but won’t spend 30 minutes a day earning certifications that can change our lives.
Master in DevOps, SRE, DevSecOps & MLOps by DevOps School!
Learn from Guru Rajesh Kumar and double your salary in just one year.
Introduction
Identity Governance & Administration (IGA) tools help organizations manage digital identities, access permissions, and user lifecycle across applications, cloud systems, and on-premises environments. Simply put, IGA ensures the right people have the right access at the right time while maintaining security, compliance, and operational efficiency.
IGA is crucial as companies adopt hybrid IT, cloud applications, and SaaS platforms. Without proper identity governance, organizations face risks such as unauthorized access, data breaches, operational inefficiencies, and regulatory non-compliance.
Real-world use cases include:
- Employee onboarding and offboarding
- Role-based access control and entitlement management
- Access certification and periodic reviews
- Privileged account governance
- Compliance reporting and audit automation
Buyers should evaluate access request workflows, role-based access, provisioning automation, policy enforcement, compliance reporting, directory integrations, MFA support, analytics, AI-driven risk detection, and deployment flexibility.
Best for: Enterprises, mid-market organizations, IT and security teams, regulated industries, and companies managing large numbers of users and applications.
Not ideal for: Very small organizations or businesses that only require basic access control or password management.
Key Trends in Identity Governance & Administration (IGA)
- AI-driven risk analytics for detecting anomalous access
- Cloud-native IGA platforms replacing legacy systems
- Integration with privileged access management
- Automated role mining and lifecycle management
- Compliance automation for GDPR, HIPAA, SOC 2, ISO 27001
- Integration with SaaS, cloud, and on-prem applications
- Adaptive access policies based on user behavior, device, and location
- Just-in-time provisioning for temporary access
- Convergence with SSO and IAM platforms
- Flexible subscription and consumption-based pricing models
How We Selected These Tools (Methodology)
- Market adoption and vendor recognition
- Feature completeness: governance, role management, lifecycle control
- Reliability and performance in enterprise and hybrid environments
- Security posture: MFA, audit logs, RBAC, encryption
- Integration capabilities with cloud, SaaS, and on-prem applications
- Suitability across company sizes and industries
- Compliance reporting and regulatory support
- AI-driven risk assessment and automation
- Deployment flexibility: cloud, hybrid, on-prem
- Documentation quality, onboarding, and professional support
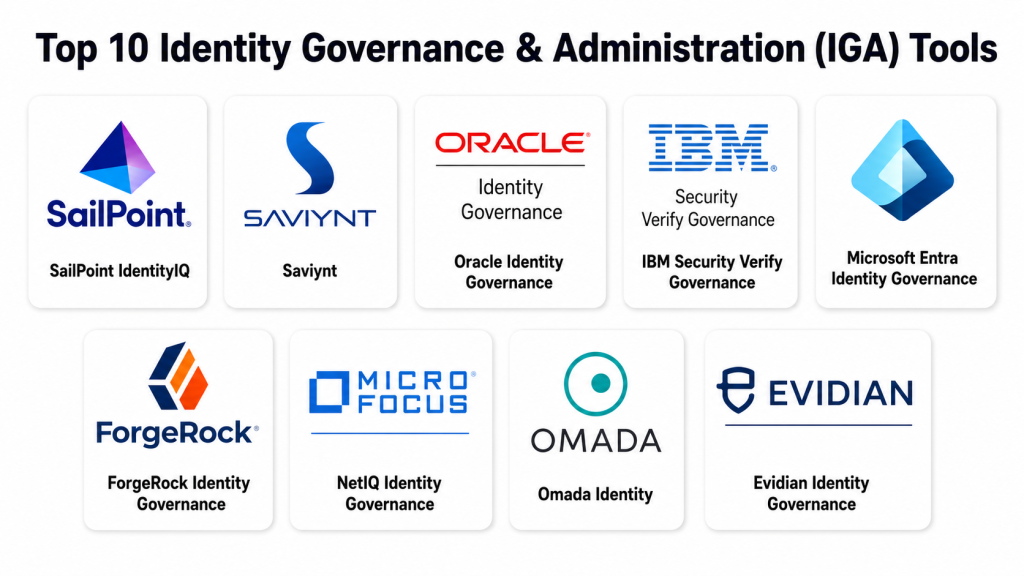
Top 10 Identity Governance & Administration (IGA) Tools
#1 — SailPoint IdentityIQ
Short description : SailPoint IdentityIQ is an enterprise IGA platform offering identity lifecycle management, access certification, and policy enforcement. It is designed for large organizations requiring granular access control and compliance reporting.
Key Features
- Automated provisioning and deprovisioning
- Role-based access control and role mining
- Access certification campaigns
- Policy enforcement and risk analytics
- Integration with cloud and on-premise systems
- Privileged account oversight
- Audit and compliance reporting
Pros
- Strong compliance and auditing capabilities
- Broad integration with enterprise systems
- Scalable for large organizations
Cons
- Complex implementation
- High administrative effort required
- Costly licensing
Platforms / Deployment
Web / Windows / Cloud / Hybrid
Security & Compliance
SSO/SAML, MFA, encryption, audit logs, RBAC, SOC 2, ISO 27001, GDPR
Integrations & Ecosystem
- Active Directory, SAP, Oracle, Salesforce
- SaaS platforms and cloud apps
- HR and ERP systems
- Privileged access management tools
- Reporting and analytics dashboards
Support & Community
Comprehensive documentation, enterprise onboarding, and active user community
#2 — Saviynt
Short description : Saviynt is a cloud-native IGA solution offering risk-based access governance, compliance automation, and AI-driven insights. It serves mid-market and enterprise organizations seeking modern governance.
Key Features
- Cloud and hybrid identity governance
- Risk-based access scoring
- Compliance and audit automation
- Role and entitlement management
- Privileged access governance
- AI-driven identity insights
- SaaS and cloud integration
Pros
- Cloud-native architecture
- Strong risk analytics
- Flexible deployment options
Cons
- Steeper learning curve
- Enterprise focus may be excessive for small teams
- Integration setup can be complex
Platforms / Deployment
Web / Cloud / Hybrid
Security & Compliance
SSO/SAML, MFA, encryption, audit logs, RBAC, GDPR, ISO 27001
Integrations & Ecosystem
- Active Directory, HR systems, ERP
- SaaS and cloud applications
- Privileged access management
- Security and SIEM tools
- Compliance reporting dashboards
Support & Community
Enterprise support, documentation, onboarding, and customer community
#3 — Oracle Identity Governance
Short description : Oracle Identity Governance provides robust user lifecycle management, role-based access control, and compliance enforcement. It is ideal for large enterprises needing integration with Oracle applications.
Key Features
- User provisioning/deprovisioning
- Role-based access and role mining
- Access certification and audit reporting
- Policy enforcement and compliance monitoring
- Integration with Oracle Cloud, SaaS, on-prem apps
- Privileged account management
- Self-service portals
Pros
- Enterprise-grade capabilities
- Deep Oracle ecosystem integration
- Strong compliance features
Cons
- Complex implementation
- High cost
- Heavy for small organizations
Platforms / Deployment
Web / Cloud / Hybrid
Security & Compliance
SSO/SAML, MFA, encryption, audit logs, RBAC, ISO 27001, GDPR, HIPAA
Integrations & Ecosystem
- Oracle Cloud apps, ERP, SaaS
- Active Directory & LDAP
- Security monitoring and SIEM platforms
- Reporting and audit dashboards
Support & Community
Enterprise support, consulting, documentation, and user communities
#4 — IBM Security Verify Governance
Short description : IBM Security Verify Governance delivers risk-based access governance, identity lifecycle management, and compliance automation. It is ideal for large enterprises requiring enterprise-grade identity governance.
Key Features
- Access request and approval workflows
- Role and entitlement management
- Automated provisioning and deprovisioning
- Compliance certification campaigns
- Risk-based access policies
- Integration with cloud and on-prem apps
- Privileged account governance
Pros
- Strong risk analytics
- Enterprise-grade security
- Broad integration ecosystem
Cons
- Complex configuration
- Steep learning curve
- Licensing can be expensive
Platforms / Deployment
Web / Cloud / Hybrid
Security & Compliance
SSO/SAML, MFA, encryption, audit logs, RBAC, SOC 2, ISO 27001, GDPR
Integrations & Ecosystem
- Active Directory, cloud apps, SaaS
- HR/ERP systems
- Privileged access tools
- Audit and reporting dashboards
Support & Community
Enterprise support, documentation, consulting services
#5 — Microsoft Entra Identity Governance
Short description : Microsoft Entra Identity Governance provides access reviews, entitlement management, and privileged identity management. Ideal for organizations using Microsoft 365 and Azure AD.
Key Features
- Access reviews and certification
- Privileged identity management
- Entitlement and role-based governance
- Integration with Azure AD and Microsoft 365
- Automated provisioning workflows
- Policy enforcement for SaaS/cloud apps
- Reporting and compliance dashboards
Pros
- Deep integration with Microsoft ecosystem
- Cloud-native and scalable
- Strong compliance reporting
Cons
- Microsoft-centric
- Premium licenses required for advanced features
- Complexity for policy management
Platforms / Deployment
Web / Windows / Cloud
Security & Compliance
SSO/SAML, MFA, encryption, audit logs, RBAC, SOC 2, ISO 27001, GDPR
Integrations & Ecosystem
- Azure AD, Microsoft 365, SaaS apps
- Cloud applications and security tools
- HR and directory integrations
Support & Community
Documentation, enterprise support, active user community
#6 — RSA Identity Governance & Lifecycle
Short description : RSA Identity Governance & Lifecycle helps enterprises automate access requests, approvals, and compliance reporting. It is designed for regulated industries and complex environments.
Key Features
- Access request and approval workflows
- Role and entitlement management
- Automated provisioning and deprovisioning
- Policy enforcement and compliance campaigns
- Integration with cloud and on-prem systems
- Privileged account management
- Risk-based access analysis
Pros
- Strong compliance and reporting
- Suitable for regulated industries
- Enterprise-scale scalability
Cons
- Complex deployment
- High admin effort
- Costly for smaller organizations
Platforms / Deployment
Web / Cloud / Hybrid
Security & Compliance
SSO/SAML, MFA, encryption, audit logs, RBAC, ISO 27001, GDPR
Integrations & Ecosystem
- Active Directory, cloud apps, SaaS
- ERP and HR systems
- Privileged access management
- Reporting and audit dashboards
Support & Community
Enterprise support, documentation, and consulting services
#7 — ForgeRock Identity Governance
Short description : ForgeRock Identity Governance manages workforce and customer identities, providing lifecycle management, access certification, and compliance enforcement.
Key Features
- Access request and approval workflows
- Automated user lifecycle
- Role and entitlement management
- Compliance certification and reporting
- Risk-based access control
- Integration with SaaS/cloud apps
- Privileged access governance
Pros
- Flexible for workforce and customer identities
- Strong cloud and hybrid support
- Risk and compliance features
Cons
- Enterprise-level complexity
- Skilled IT resources required
- Licensing cost can be high
Platforms / Deployment
Web / Cloud / Hybrid
Security & Compliance
SSO/SAML, MFA, encryption, audit logs, RBAC, SOC 2, ISO 27001, GDPR
Integrations & Ecosystem
- Active Directory, SaaS apps
- HR/ERP integrations
- Security monitoring
- Privileged access tools
Support & Community
Enterprise support, documentation, consulting services
#8 — Micro Focus NetIQ Identity Governance
Short description : NetIQ Identity Governance delivers user lifecycle management, access governance, and compliance reporting for large enterprises.
Key Features
- Access certification and reviews
- User provisioning/deprovisioning
- Role and entitlement management
- Policy enforcement and risk scoring
- Integration with cloud and on-prem apps
- Privileged account management
- Compliance reporting dashboards
Pros
- Enterprise-scale compliance support
- Suitable for complex environments
- Strong audit and reporting
Cons
- Complex deployment
- Admin learning curve
- UI may feel outdated
Platforms / Deployment
Web / Cloud / Hybrid
Security & Compliance
SSO/SAML, MFA, encryption, audit logs, RBAC, ISO 27001, GDPR
Integrations & Ecosystem
- Active Directory, SaaS apps
- ERP/HR systems
- Security monitoring
- Privileged access management
Support & Community
Documentation, enterprise support, and consulting services
#9 — Omada Identity
Short description: Omada Identity offers identity governance, access management, and compliance automation. It automates lifecycle management and simplifies regulatory reporting.
Key Features
- Access request and approval workflows
- Automated provisioning/deprovisioning
- Role and entitlement management
- Compliance certification and reporting
- Integration with cloud and on-prem apps
- Risk-based policy enforcement
- Privileged account governance
Pros
- Strong automation and lifecycle management
- Good compliance reporting
- Enterprise-focused governance
Cons
- Not ideal for small organizations
- Integration may require consulting
- Hybrid deployments can be complex
Platforms / Deployment
Web / Cloud / Hybrid
Security & Compliance
SSO/SAML, MFA, encryption, audit logs, RBAC, GDPR, ISO 27001
Integrations & Ecosystem
- Active Directory, SaaS apps
- HR/ERP integrations
- Security monitoring
- Privileged access management
Support & Community
Documentation, enterprise support, consulting services
#10 — Evidian Identity Governance
Short description: Evidian Identity Governance provides access certification, lifecycle management, and privileged account oversight for enterprises requiring compliance.
Key Features
- Access certification and reviews
- User provisioning/deprovisioning
- Role-based access control
- Risk-based access policies
- Compliance dashboards
- Cloud and on-prem integration
- Privileged account governance
Pros
- Strong automation capabilities
- Comprehensive compliance reporting
- Enterprise-focused governance
Cons
- Complex implementation
- Skilled IT resources required
- Less suitable for small organizations
Platforms / Deployment
Web / Cloud / Hybrid
Security & Compliance
SSO/SAML, MFA, encryption, audit logs, RBAC, SOC 2, ISO 27001, GDPR
Integrations & Ecosystem
- Directories: AD, LDAP
- SaaS/cloud apps
- HR/ERP integration
- Security and monitoring tools
- Privileged access management
Support & Community
Documentation, enterprise support, consulting services
Comparison Table
| Tool Name | Best For | Platform(s) Supported | Deployment | Standout Feature | Public Rating |
|---|---|---|---|---|---|
| SailPoint IdentityIQ | Large enterprises | Web | Cloud / Hybrid | Enterprise lifecycle & compliance | N/A |
| Saviynt | Mid-market & enterprise | Web | Cloud / Hybrid | Cloud-native IGA with AI insights | N/A |
| Oracle Identity Governance | Large enterprises | Web | Cloud / Hybrid | Deep Oracle ecosystem | N/A |
| IBM Security Verify Governance | Regulated enterprises | Web | Cloud / Hybrid | Risk-based access governance | N/A |
| Microsoft Entra Identity Governance | Microsoft ecosystem | Web / Windows | Cloud | Access reviews & privileged identity | N/A |
| RSA Identity Governance & Lifecycle | Regulated enterprises | Web | Cloud / Hybrid | Compliance-focused lifecycle automation | N/A |
| ForgeRock Identity Governance | Workforce & customer identity | Web | Cloud / Hybrid | Flexible cloud & hybrid support | N/A |
| Micro Focus NetIQ Identity Governance | Large enterprises | Web | Cloud / Hybrid | Enterprise-scale governance | N/A |
| Omada Identity | Enterprise lifecycle management | Web | Cloud / Hybrid | Automated user lifecycle & compliance | N/A |
| Evidian Identity Governance | Regulated enterprises | Web | Cloud / Hybrid | Access certification & privileged governance | N/A |
Evaluation & Scoring of IGA Tools
| Tool Name | Core (25%) | Ease (15%) | Integrations (15%) | Security (10%) | Performance (10%) | Support (10%) | Value (15%) | Weighted Total (0–10) |
|---|---|---|---|---|---|---|---|---|
| SailPoint IdentityIQ | 9 | 7 | 9 | 9 | 9 | 8 | 7 | 8.35 |
| Saviynt | 9 | 7 | 8 | 9 | 8 | 8 | 7 | 8.10 |
| Oracle Identity Governance | 9 | 6 | 9 | 9 | 9 | 8 | 7 | 8.15 |
| IBM Security Verify Governance | 8 | 7 | 8 | 9 | 8 | 8 | 7 | 8.00 |
| Microsoft Entra Identity Governance | 8 | 8 | 8 | 9 | 8 | 8 | 8 | 8.15 |
| RSA Identity Governance & Lifecycle | 8 | 6 | 8 | 9 | 8 | 8 | 7 | 7.85 |
| ForgeRock Identity Governance | 8 | 7 | 8 | 8 | 8 | 8 | 7 | 7.95 |
| Micro Focus NetIQ Identity Governance | 8 | 6 | 8 | 8 | 8 | 7 | 7 | 7.75 |
| Omada Identity | 8 | 7 | 8 | 8 | 8 | 7 | 7 | 7.85 |
| Evidian Identity Governance | 8 | 6 | 8 | 8 | 8 | 7 | 7 | 7.75 |
Scores are comparative. Select tools based on company size, compliance needs, integrations, and deployment flexibility.
Which IGA Tool Is Right for You?
Solo / Freelancer
Individuals rarely need full IGA suites. Lightweight identity tools or password management solutions may suffice.
SMB
Focus on cloud deployment, SaaS integration, and usability. Saviynt, Omada, and Microsoft Entra are practical choices.
Mid-Market
Prioritize access certification, automated provisioning, compliance reporting, and role management. Saviynt, IBM Verify, and ForgeRock are strong options.
Enterprise
Full lifecycle management, privileged access oversight, and regulatory compliance are essential. SailPoint, Oracle Identity Governance, RSA IGA, and ForgeRock are optimal.
Budget vs Premium
Cloud-native SaaS solutions suit budget-conscious teams; enterprise solutions provide advanced governance, analytics, and privileged access management.
Feature Depth vs Ease of Use
Enterprise solutions provide comprehensive features but require configuration. Cloud-native tools offer simpler deployment and faster adoption.
Integrations & Scalability
Check for SaaS, on-prem, HR directories, SSO, MFA, and privileged access integration. Scalability should support audits, reporting, and user lifecycle management.
Security & Compliance Needs
Evaluate encryption, MFA, RBAC, audit logs, SSO/SAML, and compliance certifications to ensure governance.
Frequently Asked Questions (FAQs)
What is IGA?
IGA manages digital identities, user access, and permissions across systems, ensuring only authorized users can access the right resources. It also helps maintain security and compliance efficiently.
Why is IGA important?
IGA prevents unauthorized access, reduces risk, enforces policies, and automates identity lifecycle management. It also supports regulatory compliance for enterprises.
How do IGA tools help compliance?
IGA tools automate access reviews, generate audit reports, and enforce segregation of duties. This ensures adherence to frameworks like GDPR, HIPAA, and SOC 2.
Can IGA integrate with cloud apps?
Yes, modern IGA solutions integrate with SaaS, cloud, and on-prem applications using APIs, SSO, and SCIM protocols. This enables unified governance across hybrid environments.
What is privileged access management?
Privileged access management controls, monitors, and audits high-risk accounts. It ensures sensitive resources are accessed only by authorized personnel.
Are IGA tools suitable for small teams?
Simplified cloud-native IGA tools can help small teams manage access efficiently. They provide essential governance without heavy infrastructure or cost.
How to select an IGA tool?
Evaluate company size, compliance needs, deployment type, integration requirements, and automation capabilities. Ensure the tool matches your organization’s security posture.
Do IGA tools include AI?
Many IGA platforms include AI-driven analytics for risk scoring, anomaly detection, and policy recommendations. This helps reduce manual errors and improves security.
Common implementation mistakes?
Mistakes include ignoring role definitions, skipping automation, failing to integrate directories, and overcomplicating policies. Proper planning is critical.
How to implement IGA successfully?
Start with a pilot deployment, define access policies, enable automation, integrate with directories, and continuously monitor compliance. Training admins is essential.
Conclusion
IGA tools are vital for securing user identities, managing access, and ensuring regulatory compliance across all systems. They provide automation, visibility, and risk mitigation for enterprises and mid-market organizations. Choosing the right tool depends on company size, complexity, and compliance requirements. Cloud-native options are simpler to deploy, while enterprise tools offer deep integration and governance. Evaluate features, integrations, and scalability before implementation. Shortlist 2–3 tools, pilot deployments, and validate governance capabilities for best results.