Upgrade & Secure Your Future with DevOps, SRE, DevSecOps, MLOps!
We spend hours scrolling social media and waste money on things we forget, but won’t spend 30 minutes a day earning certifications that can change our lives.
Master in DevOps, SRE, DevSecOps & MLOps by DevOps School!
Learn from Guru Rajesh Kumar and double your salary in just one year.
Introduction
Vulnerability Assessment Tools are specialized cybersecurity solutions that help organizations identify, evaluate, and prioritize security weaknesses across their IT environment. These tools scan applications, systems, networks, and cloud assets to detect vulnerabilities such as misconfigurations, outdated software, weak passwords, and unpatched systems. By providing actionable insights, they help security teams proactively remediate risks before attackers exploit them.
In today’s cybersecurity landscape, threats are increasingly sophisticated, targeting hybrid and cloud infrastructures, IoT devices, and critical applications. Organizations require comprehensive visibility into their attack surface to maintain compliance, reduce risk exposure, and protect sensitive data. Vulnerability assessment tools are integral for both preventive security measures and regulatory adherence.
Common use cases include vulnerability scanning, asset discovery, patch management prioritization, compliance audits, penetration testing support, cloud environment assessment, and risk reporting for executives.
Buyers should evaluate: scanning depth, frequency, asset coverage, integration with patch and ticketing systems, reporting capabilities, compliance support, ease of use, automation features, scalability, and cost-effectiveness.
Best for: Security teams, IT departments, compliance officers, enterprises with complex IT infrastructure, MSPs, and organizations in regulated industries.
Not ideal for: Small businesses without dedicated IT security staff, organizations with minimal digital footprint, or teams that only need basic endpoint protection.
Key Trends in Vulnerability Assessment Tools
AI-driven vulnerability detection for faster and more accurate identification.
- Integration with automated patch management and configuration tools.
- Continuous vulnerability monitoring for hybrid and cloud-native environments.
- API-based integrations with SIEM, SOAR, ITSM, and DevOps pipelines.
- Focus on compliance automation and regulatory reporting.
- Risk-based prioritization using threat intelligence feeds.
- Cloud-native scanning with container and Kubernetes environment support.
- Subscription-based and consumption-based pricing models.
- Emphasis on reducing false positives with machine learning.
- Low-code/no-code playbooks for remediation guidance.
How We Selected These Tools (Methodology)
- Market adoption and credibility across enterprises and SMEs.
- Feature completeness including scanning, reporting, and remediation guidance.
- Accuracy and reliability of vulnerability detection.
- Security posture and adherence to compliance frameworks.
- Integration with existing security, IT, and DevOps tools.
- Coverage across network, cloud, endpoint, and web application assets.
- Ease of deployment, user interface, and workflow customization.
- Vendor support quality and community engagement.
- Scalability for growing IT environments.
- Continuous innovation and AI-driven features.
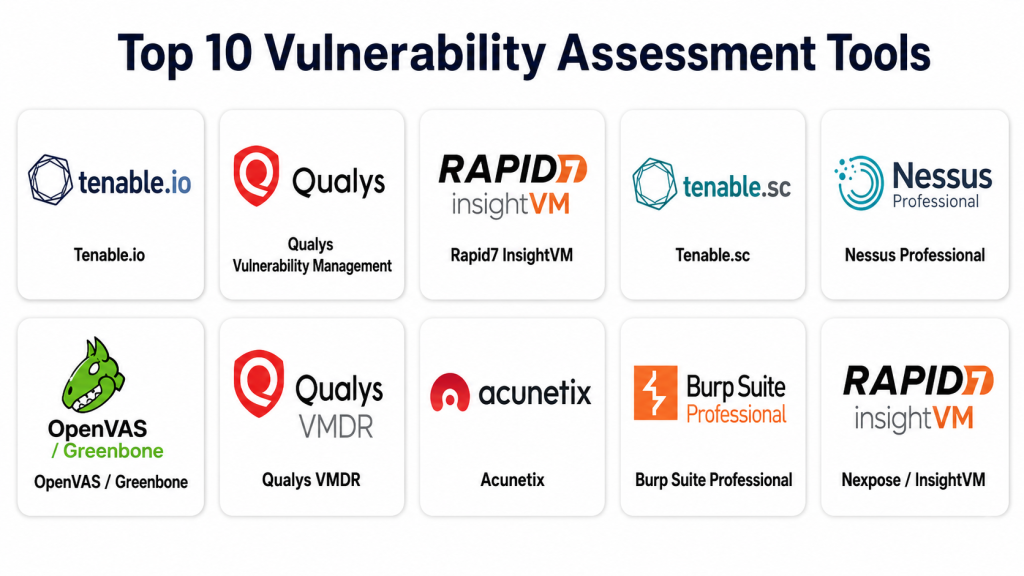
Top 10 Vulnerability Assessment Tools
#1 — Tenable.io
Short description : Tenable.io is a cloud-based vulnerability management platform designed for enterprises to identify and prioritize risks across assets and cloud environments. It is ideal for organizations seeking continuous vulnerability visibility, automated reporting, and compliance tracking. Tenable.io integrates well with modern IT and DevOps environments.
Key Features
- Continuous vulnerability scanning
- Asset discovery and inventory
- Risk-based prioritization
- Cloud and container support
- Compliance reporting and dashboards
- API integrations for automation
- Customizable alerts and notifications
Pros
- Strong cloud and hybrid coverage
- Excellent reporting and dashboards
- Integrates with DevOps and IT workflows
Cons
- Subscription pricing can be high for smaller teams
- Learning curve for new users
- Advanced features require training
Platforms / Deployment
Web / Cloud
Security & Compliance
SSO/SAML, MFA, encryption, audit logs, RBAC, SOC 2, ISO 27001, GDPR
Integrations & Ecosystem
Integrates with SIEM, ITSM, patch management, cloud platforms, and DevOps pipelines.
- ServiceNow, Jira
- AWS, Azure, GCP
- EDR/endpoint solutions
- APIs for custom workflows
- Security dashboards
Support & Community
Enterprise support, documentation, knowledge base, training, and active user community.
#2 — Qualys Vulnerability Management
Short description : Qualys Vulnerability Management is a cloud-based tool for continuous scanning and assessment across IT assets. It is designed for enterprises and compliance-focused organizations to detect vulnerabilities, monitor threats, and generate audit-ready reports. Qualys supports multi-environment scanning including endpoints, servers, and cloud workloads.
Key Features
- Continuous network, endpoint, and cloud scanning
- Risk scoring and prioritization
- Patch assessment and guidance
- Compliance reporting (PCI DSS, ISO)
- Web application scanning
- API-driven automation
- Integration with ticketing and patching systems
Pros
- Broad coverage across hybrid environments
- Strong reporting and compliance features
- Mature enterprise platform
Cons
- User interface may be complex for beginners
- Some advanced modules require separate licensing
- Requires tuning for optimal results
Platforms / Deployment
Web / Cloud
Security & Compliance
SSO/SAML, MFA, encryption, audit logs, RBAC, SOC 2, ISO 27001, HIPAA, GDPR
Integrations & Ecosystem
Integrates with SIEM, SOAR, ITSM, patch management, and DevOps tools.
- ServiceNow, Jira
- Splunk, QRadar
- Cloud platforms (AWS, Azure, GCP)
- API for automation
- Ticketing systems
Support & Community
Enterprise support, documentation, training, and partner ecosystem.
#3 — Rapid7 InsightVM
Short description: InsightVM is Rapid7’s cloud-based vulnerability assessment tool, designed to provide real-time risk visibility and remediation guidance. It helps security teams prioritize threats, track remediation progress, and integrate insights with operational workflows. Ideal for SOC teams and IT operations managing large hybrid environments.
Key Features
- Real-time vulnerability scanning
- Risk scoring and prioritization
- Live dashboards for remediation tracking
- Cloud and container security
- Threat intelligence integration
- API automation and integrations
- Reporting and compliance tools
Pros
- Interactive dashboards and metrics
- Strong integration capabilities
- Risk-based approach simplifies prioritization
Cons
- Subscription costs may be high
- Requires training for advanced features
- Cloud dependency may concern some environments
Platforms / Deployment
Web / Cloud
Security & Compliance
SSO/SAML, MFA, encryption, audit logs, RBAC, SOC 2, ISO 27001, GDPR
Integrations & Ecosystem
Integrates with SIEM, ITSM, patch management, and cloud tools.
- ServiceNow, Jira
- AWS, Azure, GCP
- Endpoint solutions
- APIs for automation
- Security dashboards
Support & Community
Enterprise support, documentation, training, and active Rapid7 community.
#4 — Tenable.sc
Short description : Tenable.sc provides on-premise vulnerability management for enterprises that require detailed analytics, compliance reporting, and historical trend tracking. It is ideal for organizations with sensitive data or strict regulatory requirements, offering deep insight into on-prem and hybrid IT environments.
Key Features
- Network and host scanning
- Compliance reporting (PCI DSS, ISO, HIPAA)
- Risk-based prioritization
- Historical vulnerability trending
- Integration with SIEM and patching tools
- Customizable dashboards
- Threat intelligence feeds
Pros
- Detailed analytics and reporting
- On-prem flexibility
- Strong regulatory compliance support
Cons
- Complex deployment
- Requires skilled administrators
- Higher operational overhead
Platforms / Deployment
Web / Self-hosted / Hybrid
Security & Compliance
SSO/SAML, MFA, encryption, audit logs, RBAC, SOC 2, ISO 27001, GDPR
Integrations & Ecosystem
- SIEM platforms
- Patch management systems
- Ticketing systems
- Cloud connectors
- API-driven integrations
Support & Community
Enterprise support, partner network, documentation, and training programs.
#5 — Nessus Professional
Short description : Nessus Professional is a widely used vulnerability scanner for IT environments. It is suitable for security analysts and penetration testers to identify network, host, and application vulnerabilities. Nessus provides detailed reports and remediation guidance, making it effective for both proactive and compliance-driven use cases.
Key Features
- Network and host vulnerability scanning
- Compliance checks
- Prebuilt and customizable templates
- Plugin updates for emerging threats
- Reporting and remediation guidance
- Multi-platform support
- API access for integrations
Pros
- Easy to deploy and use
- Strong plugin ecosystem
- Accurate detection for common vulnerabilities
Cons
- Limited scalability for large enterprises
- Focused on scanning rather than full risk management
- Lacks integrated workflow automation
Platforms / Deployment
Windows / macOS / Linux / Web
Security & Compliance
Not publicly stated; supports local encryption and access controls.
Integrations & Ecosystem
- SIEM connectors
- Patch management systems
- ITSM platforms
- APIs for automation
- Security dashboards
Support & Community
Documentation, enterprise support, and active Nessus user community.
#6 — OpenVAS / Greenbone
Short description: OpenVAS, maintained by Greenbone, is an open-source vulnerability assessment tool suitable for enterprises and SMBs. It provides scanning for network and system vulnerabilities and integrates with other security tools. Ideal for cost-conscious teams seeking customizable, open-source solutions.
Key Features
- Network and host scanning
- Open-source vulnerability feeds
- Risk scoring and prioritization
- Reporting and alerting
- API for integrations
- Multi-platform support
- Community plugin updates
Pros
- Free and open-source
- Customizable scanning
- Active community
Cons
- Requires setup and configuration
- Less polished interface than commercial tools
- Support is community-based
Platforms / Deployment
Windows / macOS / Linux / Web
Security & Compliance
Varies / N/A
Integrations & Ecosystem
- SIEM connectors
- ITSM tools
- Ticketing systems
- APIs for custom workflows
- Security dashboards
Support & Community
Community support, documentation, and forums.
#7 — Qualys VMDR
Short description : Qualys VMDR (Vulnerability Management, Detection, and Response) integrates vulnerability scanning with patching workflows and threat intelligence. It is designed for enterprises needing end-to-end vulnerability lifecycle management across IT and cloud environments.
Key Features
- Continuous scanning and asset discovery
- Patch prioritization
- Threat intelligence-driven risk scoring
- Compliance reporting
- API automation
- Dashboard visualization
- Multi-platform support
Pros
- End-to-end vulnerability lifecycle
- Strong cloud coverage
- Integration with patch management
Cons
- Licensing can be expensive
- Interface may be complex for new users
- Advanced features require training
Platforms / Deployment
Web / Cloud
Security & Compliance
SSO/SAML, MFA, encryption, audit logs, RBAC, SOC 2, ISO 27001, GDPR
Integrations & Ecosystem
- Patch management
- SIEM and SOAR
- Cloud platforms
- API-driven workflows
- Ticketing systems
Support & Community
Enterprise support, documentation, training, and user community.
#8 — Acunetix
Short description : Acunetix is a web application vulnerability scanner that helps detect common and advanced security flaws in websites and APIs. It is ideal for developers, penetration testers, and security teams focused on application-layer vulnerabilities.
Key Features
- Web and API scanning
- SQLi, XSS, and OWASP Top 10 detection
- Automated crawling and scanning
- Reporting and remediation guidance
- Integration with CI/CD pipelines
- API for workflow automation
- Compliance reports
Pros
- Focused on application security
- Automation reduces manual testing
- Integrates with DevOps workflows
Cons
- Limited to web and API scope
- Does not scan network/host vulnerabilities
- Enterprise features require license
Platforms / Deployment
Windows / Linux / Web
Security & Compliance
Not publicly stated
Integrations & Ecosystem
- CI/CD tools (Jenkins, GitLab)
- Bug trackers (Jira)
- APIs for automation
- Reporting dashboards
Support & Community
Documentation, enterprise support, training, and user forums.
#9 — Burp Suite Professional
Short description: Burp Suite Professional is a web application security testing tool for vulnerability assessment and penetration testing. Security analysts and developers use it to detect security flaws, perform manual testing, and verify application security posture.
Key Features
- Web vulnerability scanning
- Manual and automated testing
- Extensible with plugins
- Reporting and remediation guidance
- API scanning capabilities
- Integration with CI/CD pipelines
- Active security testing community
Pros
- Strong testing capabilities
- Widely adopted by security professionals
- Flexible and extensible
Cons
- Requires technical expertise
- Focused only on web apps
- Manual testing needed for full coverage
Platforms / Deployment
Windows / macOS / Linux
Security & Compliance
Not publicly stated
Integrations & Ecosystem
- CI/CD pipelines
- Bug trackers
- Custom plugins
- APIs for automation
- Security dashboards
Support & Community
Documentation, training resources, and active security community.
#10 — Nexpose / InsightVM
Short description: Nexpose, integrated into Rapid7 InsightVM, offers vulnerability scanning, risk prioritization, and remediation guidance. It is suitable for enterprises seeking continuous visibility into network and system vulnerabilities and actionable insights for remediation.
Key Features
- Continuous network scanning
- Risk scoring and prioritization
- Patch management integration
- Reporting and dashboards
- Asset discovery and classification
- API-based workflow automation
- Compliance reporting
Pros
- Real-time risk visibility
- Strong remediation guidance
- Integration with other Rapid7 tools
Cons
- Learning curve for advanced features
- Cloud dependency for some modules
- Licensing can be complex
Platforms / Deployment
Web / Cloud / Hybrid
Security & Compliance
SSO/SAML, MFA, encryption, audit logs, RBAC, SOC 2, ISO 27001, GDPR
Integrations & Ecosystem
- SIEM platforms
- Patch management
- ITSM and ticketing
- Cloud and endpoint platforms
- API for workflow automation
- Security dashboards
Support & Community
Enterprise support, documentation, training, and active user community.
Comparison Table (Top 10)
| Tool Name | Best For | Platform(s) Supported | Deployment | Standout Feature | Public Rating |
|---|---|---|---|---|---|
| Tenable.io | Cloud & hybrid environments | Web | Cloud | Continuous vulnerability visibility | N/A |
| Qualys VM | Compliance-focused enterprises | Web | Cloud | Multi-environment scanning & reporting | N/A |
| Rapid7 InsightVM | SOC & IT teams | Web | Cloud | Real-time risk visibility | N/A |
| Tenable.sc | On-prem & hybrid environments | Web | Self-hosted / Hybrid | Detailed analytics & trend tracking | N/A |
| Nessus Professional | Security analysts | Windows/macOS/Linux | Self-hosted | Accurate host & network scanning | N/A |
| OpenVAS / Greenbone | Open-source & customizable | Windows/macOS/Linux | Self-hosted | Free & open-source scanning | N/A |
| Qualys VMDR | Patch & risk-focused enterprises | Web | Cloud | End-to-end vulnerability lifecycle | N/A |
| Acunetix | Web & API security teams | Windows/Linux/Web | Web | Automated web vulnerability scanning | N/A |
| Burp Suite Professional | Security testers & developers | Windows/macOS/Linux | Self-hosted | Manual & automated web testing | N/A |
| Nexpose / InsightVM | Enterprise vulnerability management | Web | Cloud / Hybrid | Risk prioritization & remediation | N/A |
Evaluation & Scoring of Vulnerability Assessment Tools
| Tool Name | Core (25%) | Ease (15%) | Integrations (15%) | Security (10%) | Performance (10%) | Support (10%) | Value (15%) | Weighted Total |
|---|---|---|---|---|---|---|---|---|
| Tenable.io | 9 | 8 | 9 | 9 | 9 | 8 | 8 | 8.85 |
| Qualys VM | 9 | 7 | 8 | 9 | 8 | 8 | 7 | 8.05 |
| Rapid7 InsightVM | 8 | 8 | 8 | 8 | 8 | 8 | 8 | 8.00 |
| Tenable.sc | 9 | 7 | 8 | 9 | 9 | 8 | 7 | 8.10 |
| Nessus Professional | 8 | 9 | 7 | 8 | 8 | 8 | 7 | 7.95 |
| OpenVAS / Greenbone | 7 | 7 | 7 | 7 | 7 | 7 | 8 | 7.25 |
| Qualys VMDR | 9 | 8 | 8 | 9 | 8 | 8 | 7 | 8.15 |
| Acunetix | 8 | 8 | 7 | 8 | 8 | 8 | 7 | 7.90 |
| Burp Suite Professional | 8 | 7 | 7 | 8 | 8 | 8 | 7 | 7.70 |
| Nexpose / InsightVM | 8 | 8 | 8 | 8 | 8 | 8 | 7 | 7.95 |
Interpretation: Scores are comparative. Higher scores indicate broader coverage, better integration, and usability. Organizations should consider SOC size, cloud vs on-prem requirements, and regulatory compliance when selecting a tool.
Which Vulnerability Assessment Tool Is Right for You?
Solo / Freelancer
Tools like Nessus Professional or Burp Suite are sufficient for individual testers or consultants needing targeted scanning.
SMB
OpenVAS / Greenbone or Acunetix offer cost-effective, easy-to-deploy scanning for small to medium environments.
Mid-Market
Rapid7 InsightVM, Qualys VM, and Tenable.io provide scalable solutions with dashboards, risk scoring, and integrations suitable for growing IT environments.
Enterprise
Tenable.sc, Tenable.io, Qualys VMDR, and Nexpose are recommended for large organizations requiring advanced analytics, hybrid visibility, compliance reporting, and enterprise support.
Budget vs Premium
Budget-conscious teams may prioritize open-source tools or single-purpose scanners, while premium platforms provide broader coverage, automation, and centralized reporting.
Feature Depth vs Ease of Use
Visual dashboards and prebuilt reporting simplify use (Rapid7, Tenable.io), while deeper analytics and customization benefit enterprise SOCs (Tenable.sc, Qualys VMDR).
Integrations & Scalability
Ensure the tool integrates with SIEM, SOAR, patch management, ticketing, and DevOps pipelines. Scalability is key for organizations with hybrid or cloud assets.
Security & Compliance Needs
Enterprise and regulated organizations should prioritize tools with SOC 2, ISO 27001, GDPR, HIPAA support, audit trails, and RBAC controls.
Frequently Asked Questions (FAQs)
What is a Vulnerability Assessment Tool?
A tool that scans IT systems, networks, applications, and cloud assets for security weaknesses, providing actionable insights to mitigate risks.
How does it differ from penetration testing?
Vulnerability assessment identifies potential weaknesses; penetration testing actively exploits them to evaluate security impact.
Can these tools scan cloud environments?
Yes, most modern tools support cloud infrastructure, containers, and hybrid environments.
How often should I run scans?
Continuous scanning is ideal, especially for dynamic cloud environments. At minimum, monthly or quarterly scans are recommended.
Are vulnerability assessments sufficient for compliance?
They help but must be combined with remediation, patching, and reporting to meet regulatory requirements.
Do these tools prioritize critical vulnerabilities?
Most provide risk-based scoring to help teams address high-impact issues first.
Can they integrate with patch management?
Yes, many tools offer integrations or automation to coordinate patching with detected vulnerabilities.
Are open-source tools effective?
OpenVAS/Greenbone can be effective for SMBs or tech-savvy teams but may require more configuration and maintenance.
What is the difference between Tenable.io and Tenable.sc?
Tenable.io is cloud-based, while Tenable.sc is on-premise, providing deeper analytics for controlled environments.
How do these tools reduce cyber risk?
By identifying, scoring, and tracking vulnerabilities, these tools allow organizations to remediate issues proactively before attackers exploit them.
Conclusion
Vulnerability Assessment Tools are critical for proactively identifying and mitigating IT security risks. The best tool depends on organizational size, cloud vs on-prem infrastructure, regulatory requirements, and SOC maturity. SMBs may find OpenVAS, Nessus, or Acunetix suitable, while mid-market and enterprises benefit from Rapid7, Tenable.io, Qualys VM, or Tenable.sc. Key next steps include shortlisting 2–3 tools, evaluating integration capabilities, running pilot scans, and validating remediation workflows to ensure comprehensive risk reduction and compliance readiness.