Upgrade & Secure Your Future with DevOps, SRE, DevSecOps, MLOps!
We spend hours scrolling social media and waste money on things we forget, but won’t spend 30 minutes a day earning certifications that can change our lives.
Master in DevOps, SRE, DevSecOps & MLOps by DevOps School!
Learn from Guru Rajesh Kumar and double your salary in just one year.
Introduction
Service Mesh Platforms help teams manage communication between microservices in a secure, observable, and controlled way. In simple words, when many services talk to each other inside a Kubernetes or cloud-native environment, a service mesh adds a dedicated layer for traffic routing, encryption, identity, retries, load balancing, monitoring, and policy enforcement.
Service mesh matters because modern applications are often built from many small services. Without proper control, teams may struggle with service-to-service security, traffic failures, debugging, latency, dependency visibility, and zero-trust enforcement.
Common use cases include secure microservice communication, traffic splitting, canary releases, mTLS encryption, service observability, multi-cluster networking, API reliability, and policy-based access control.
Buyers should evaluate ease of adoption, Kubernetes compatibility, traffic management, security controls, observability, performance overhead, multi-cluster support, ecosystem maturity, developer experience, support quality, and operational complexity.
Best for: DevOps teams, SRE teams, platform engineering teams, cloud-native teams, Kubernetes administrators, security teams, enterprise architects, SaaS companies, and organizations running microservices at scale.
Not ideal for: small teams with simple monolithic applications, early-stage projects with only a few services, or teams without Kubernetes and service networking skills. In those cases, an ingress controller, API gateway, or simpler networking approach may be enough.
Key Trends in Service Mesh Platforms
- Zero-trust service networking is becoming a major driver, especially for teams that need service identity, encrypted traffic, and policy-based communication.
- Sidecarless and ambient mesh models are gaining attention, because many teams want service mesh benefits with lower operational overhead and reduced resource usage.
- Multi-cluster service mesh adoption is increasing, especially for organizations running workloads across multiple Kubernetes clusters, regions, or cloud providers.
- Observability is becoming a core service mesh value, with metrics, traces, logs, traffic topology, and service dependency maps helping teams troubleshoot faster.
- GitOps-driven mesh configuration is becoming common, allowing teams to manage routing rules, policies, and traffic behavior through version-controlled workflows.
- Security teams are more involved in mesh decisions, especially where mTLS, access control, identity, and audit requirements are important.
- Gateway and mesh integration is becoming stronger, because teams want consistent traffic control across north-south and east-west communication.
- Performance overhead is under closer review, as teams compare sidecar-based, proxy-based, and lightweight mesh approaches.
- Platform teams are standardizing service mesh usage, creating reusable policies, templates, and guardrails so developers do not manage every detail manually.
- AI-assisted operations may support mesh troubleshooting, especially by helping correlate service failures, latency spikes, and traffic anomalies across distributed systems.
How We Selected These Tools
The tools below were selected using practical buyer-focused evaluation logic:
- Market adoption and recognition across Kubernetes, microservices, service networking, and cloud-native environments.
- Feature completeness for traffic management, service discovery, encryption, policy control, observability, and resilience.
- Security posture signals such as mTLS, identity, authorization policies, RBAC, audit visibility, and access control.
- Reliability and performance signals for production-grade service communication.
- Integration strength with Kubernetes, ingress gateways, API gateways, observability tools, CI/CD platforms, GitOps workflows, and cloud infrastructure.
- Fit across customer types, including startups, SMBs, mid-market teams, enterprises, and regulated organizations.
- Ease of installation, day-to-day operations, debugging, and upgrade management.
- Flexibility across single-cluster, multi-cluster, hybrid, and cloud-native environments.
- Community maturity, documentation quality, commercial support, and ecosystem strength.
- Practical value based on feature depth, usability, security, and operational fit.
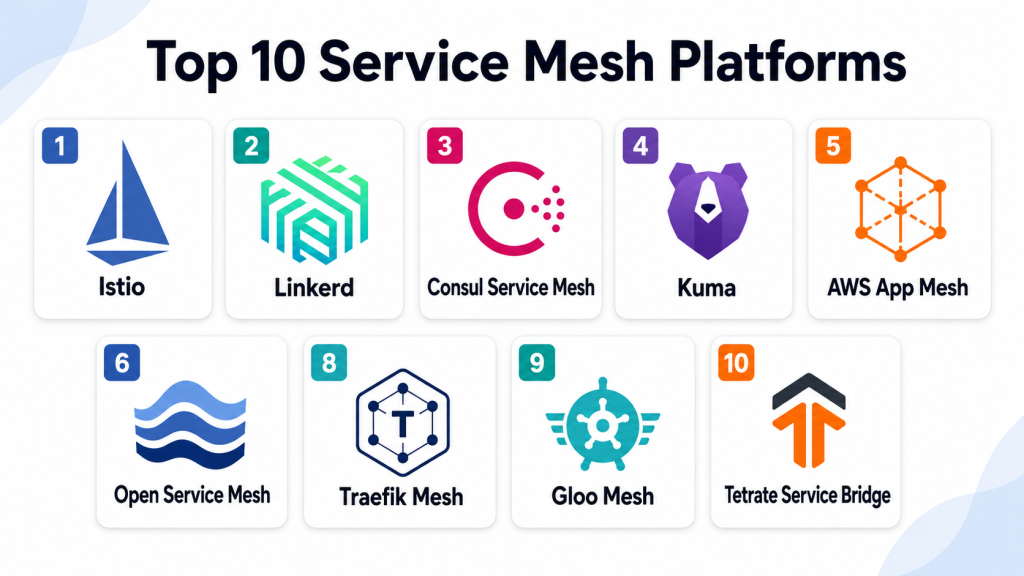
Top 10 Service Mesh Platforms
#1 — Istio
Short description: Istio is one of the most widely recognized service mesh platforms for Kubernetes and microservices. It helps teams manage traffic, security, observability, and policy across distributed applications.
Key Features
- Service-to-service traffic management.
- mTLS-based service communication.
- Traffic splitting, retries, timeouts, and fault injection.
- Authorization policies and access controls.
- Observability through metrics, logs, and traces.
- Gateway integration for ingress and egress control.
- Multi-cluster support depending on architecture.
Pros
- Strong feature depth for enterprise microservices.
- Large ecosystem and community adoption.
- Good fit for complex Kubernetes environments.
Cons
- Can be complex for beginners.
- Requires careful configuration and operational maturity.
- Performance overhead should be tested before large rollout.
Platforms / Deployment
Web / Linux-based Kubernetes environments
Cloud / Self-hosted / Hybrid
Security & Compliance
Supports mTLS, workload identity, authorization policies, RBAC through Kubernetes, audit visibility through integrations, and encrypted service communication. Specific compliance certifications are deployment-dependent and should be verified with vendors or hosting providers.
Integrations & Ecosystem
Istio integrates deeply with Kubernetes and common cloud-native tools. It is widely used with observability, gateway, policy, and GitOps workflows.
- Kubernetes
- Envoy proxy
- Prometheus
- Grafana
- Jaeger
- GitOps tools
Support & Community
Istio has strong open-source community support, extensive documentation, vendor-backed distributions, training resources, and a mature cloud-native ecosystem.
#2 — Linkerd
Short description: Linkerd is a lightweight service mesh focused on simplicity, security, and performance. It is often chosen by teams that want service mesh benefits without heavy operational complexity.
Key Features
- Automatic mTLS for service-to-service communication.
- Lightweight proxy architecture.
- Service metrics and golden signal visibility.
- Traffic splitting for progressive delivery.
- Kubernetes-native installation and management.
- Low operational overhead compared with heavier meshes.
- Multi-cluster capabilities depending on setup.
Pros
- Simple and approachable service mesh experience.
- Lightweight and performance-conscious.
- Good fit for teams new to service mesh.
Cons
- Feature set may be less broad than some enterprise meshes.
- Advanced traffic control may require careful validation.
- Ecosystem may be smaller than larger alternatives.
Platforms / Deployment
Web / Linux-based Kubernetes environments
Cloud / Self-hosted / Hybrid
Security & Compliance
Supports automatic mTLS, identity-based service communication, encrypted traffic, and Kubernetes-based access controls. Specific compliance certifications are not publicly stated as a universal platform claim.
Integrations & Ecosystem
Linkerd integrates well with Kubernetes and common cloud-native observability tools. It is useful for teams that want secure service communication with fewer moving parts.
- Kubernetes
- Prometheus
- Grafana
- Jaeger
- Flagger
- GitOps workflows
Support & Community
Linkerd has open-source documentation, community support, and commercial ecosystem options depending on vendor and deployment needs.
#3 — Consul Service Mesh
Short description: Consul Service Mesh provides service discovery, service networking, and secure service-to-service communication across Kubernetes, virtual machines, and hybrid environments. It is best for teams running mixed infrastructure.
Key Features
- Service discovery across multiple environments.
- Service mesh with mTLS.
- Support for Kubernetes and non-Kubernetes workloads.
- Intentions-based access control.
- Multi-datacenter and hybrid networking capabilities.
- Integration with HashiCorp ecosystem tools.
- Traffic management and service routing features.
Pros
- Strong for hybrid infrastructure.
- Good fit for teams using HashiCorp tools.
- Works beyond Kubernetes-only environments.
Cons
- Requires understanding of Consul architecture.
- Kubernetes-only teams may prefer simpler mesh options.
- Enterprise features and support should be reviewed carefully.
Platforms / Deployment
Web / Linux / Kubernetes / Virtual machine environments
Cloud / Self-hosted / Hybrid
Security & Compliance
Supports mTLS, service identity, access intentions, ACLs, encryption options, and policy-based communication. Specific compliance certifications depend on product edition and deployment.
Integrations & Ecosystem
Consul Service Mesh is strong in environments using infrastructure automation, secrets management, service discovery, and multi-platform workloads.
- Kubernetes
- Virtual machines
- Nomad
- Vault
- Terraform
- Monitoring tools
Support & Community
Consul has strong documentation, community support, enterprise support options through the vendor ecosystem, and broad adoption among infrastructure teams.
#4 — Kuma
Short description: Kuma is a service mesh platform built on Envoy that supports Kubernetes and universal workloads. It is suitable for teams that need service mesh across both Kubernetes and traditional infrastructure.
Key Features
- Kubernetes and universal mode support.
- Envoy-based data plane.
- mTLS for service-to-service communication.
- Traffic routing and resilience policies.
- Multi-zone and multi-mesh capabilities.
- Observability integrations.
- Policy-driven mesh management.
Pros
- Flexible for Kubernetes and non-Kubernetes environments.
- Good multi-zone architecture.
- Useful for organizations with mixed infrastructure.
Cons
- Requires mesh and proxy knowledge.
- Smaller ecosystem than Istio in some environments.
- Advanced setup needs careful planning.
Platforms / Deployment
Web / Linux / Kubernetes / Virtual machine environments
Cloud / Self-hosted / Hybrid
Security & Compliance
Supports mTLS, service identity, policy-based traffic control, access rules, and encrypted service communication. Specific compliance certifications should be verified with the vendor or deployment provider.
Integrations & Ecosystem
Kuma works well with Envoy-based networking and cloud-native observability stacks. It can support both containerized and traditional workloads.
- Kubernetes
- Envoy proxy
- Prometheus
- Grafana
- Kong ecosystem tools
- Hybrid infrastructure
Support & Community
Kuma provides documentation, community support, and commercial ecosystem options depending on vendor and deployment model.
#5 — AWS App Mesh
Short description: AWS App Mesh is a service mesh designed for applications running on AWS infrastructure. It helps teams manage service-to-service communication across supported AWS compute environments using Envoy-based proxies.
Key Features
- Service-to-service traffic control.
- Envoy-based proxy support.
- Integration with AWS compute services.
- Traffic routing, retries, and timeouts.
- Observability integration with AWS monitoring tools.
- Support for microservices across supported AWS environments.
- Centralized mesh configuration through AWS controls.
Pros
- Strong fit for AWS-centered teams.
- Integrates naturally with AWS services.
- Useful for cloud-native AWS microservices.
Cons
- Best suited for AWS environments.
- Less flexible for non-AWS multi-cloud strategies.
- Requires AWS networking and service architecture knowledge.
Platforms / Deployment
Web / Linux-based workloads / Kubernetes support through AWS environments
Cloud
Security & Compliance
Supports encrypted communication patterns depending on configuration, AWS identity and access controls, and integration with AWS security services. Specific compliance coverage depends on AWS configuration and customer requirements.
Integrations & Ecosystem
AWS App Mesh works best inside AWS environments where services already use AWS compute, monitoring, and networking services.
- Amazon Elastic Kubernetes Service
- Amazon Elastic Container Service
- AWS compute services
- AWS monitoring tools
- AWS identity services
- Envoy proxy
Support & Community
AWS provides documentation, support plans, partner resources, and cloud practitioner expertise. Community usage is strongest among AWS-native teams.
#6 — Open Service Mesh
Short description: Open Service Mesh is an open-source service mesh built around Envoy and focused on Kubernetes service-to-service communication. It is useful for teams exploring lightweight service mesh patterns.
Key Features
- Kubernetes-native service mesh.
- Envoy-based proxy architecture.
- mTLS support for service communication.
- Traffic access control policies.
- Observability integrations.
- Simple service mesh operations.
- Open-source project model.
Pros
- Lightweight service mesh approach.
- Kubernetes-focused and open-source.
- Useful for teams exploring service mesh concepts.
Cons
- Ecosystem maturity should be validated for production needs.
- Feature depth may not match larger meshes.
- Long-term support should be reviewed carefully.
Platforms / Deployment
Web / Linux-based Kubernetes environments
Self-hosted / Cloud / Hybrid
Security & Compliance
Supports mTLS, service identity, access control policies, and encrypted service communication depending on configuration. Compliance certifications are not publicly stated as a universal platform claim.
Integrations & Ecosystem
Open Service Mesh fits Kubernetes environments where teams want service mesh capabilities with Envoy-based architecture.
- Kubernetes
- Envoy proxy
- Prometheus
- Grafana
- CI/CD workflows
- Cloud-native observability tools
Support & Community
Support is mainly open-source and community-driven unless adopted through a vendor-backed environment. Documentation and ecosystem maturity should be evaluated before production adoption.
#7 — Cilium Service Mesh
Short description: Cilium Service Mesh extends Cilium’s eBPF-powered networking and security capabilities into service mesh use cases. It is suitable for teams that want strong networking, observability, and security with modern Kubernetes infrastructure.
Key Features
- eBPF-based networking and security foundation.
- Service mesh capabilities without traditional sidecar dependency in some modes.
- Kubernetes network policy enforcement.
- Service visibility and observability.
- mTLS support depending on configuration.
- Gateway and ingress-related capabilities depending on setup.
- Strong networking and security integration.
Pros
- Modern eBPF-based architecture.
- Strong networking, security, and observability foundation.
- Useful for performance-conscious Kubernetes teams.
Cons
- Requires networking and Kubernetes expertise.
- Feature use depends on architecture and configuration.
- Teams should validate service mesh maturity for their exact needs.
Platforms / Deployment
Web / Linux-based Kubernetes environments
Cloud / Self-hosted / Hybrid
Security & Compliance
Supports network policy, service identity features, encryption options depending on configuration, observability, and security enforcement. Specific compliance certifications should be verified with the vendor or deployment provider.
Integrations & Ecosystem
Cilium integrates strongly with Kubernetes networking, observability, and cloud-native security workflows.
- Kubernetes
- eBPF-based networking
- Hubble observability
- Prometheus
- Grafana
- Gateway API workflows
Support & Community
Cilium has a strong cloud-native community, growing enterprise adoption, documentation, and commercial support options depending on vendor ecosystem.
#8 — Traefik Mesh
Short description: Traefik Mesh is a lightweight service mesh connected to the broader Traefik ecosystem. It is useful for teams that want simpler service discovery, observability, and traffic management in Kubernetes environments.
Key Features
- Kubernetes-native service mesh capabilities.
- Lightweight service communication management.
- Service discovery support.
- Traffic routing and observability features.
- Integration with Traefik ecosystem.
- Simple installation and usage model.
- API and ingress-adjacent workflows depending on setup.
Pros
- Lightweight and approachable.
- Good fit for teams already using Traefik.
- Simpler than heavier enterprise meshes.
Cons
- Feature depth may be limited for complex enterprise needs.
- Smaller ecosystem compared with Istio.
- Production fit should be validated carefully.
Platforms / Deployment
Web / Linux-based Kubernetes environments
Cloud / Self-hosted / Hybrid
Security & Compliance
Supports secure service communication features depending on configuration. Detailed enterprise compliance claims, SSO, RBAC, and audit capabilities are not publicly stated as universal platform claims.
Integrations & Ecosystem
Traefik Mesh fits teams that want service mesh functionality close to ingress, API, and Kubernetes routing workflows.
- Kubernetes
- Traefik Proxy
- Traefik ecosystem tools
- Observability tools
- GitOps workflows
- Cloud-native routing workflows
Support & Community
Traefik has documentation, community resources, and commercial support options depending on product and vendor offering.
#9 — Gloo Mesh
Short description: Gloo Mesh is an enterprise service mesh management platform built around Istio and Envoy-based service networking. It is designed for organizations that need multi-cluster, multi-cloud, and enterprise-grade mesh operations.
Key Features
- Multi-cluster service mesh management.
- Istio-based service mesh operations.
- Centralized policy control.
- Traffic management and routing.
- Observability and service visibility.
- Zero-trust service networking features.
- Enterprise governance across mesh environments.
Pros
- Strong fit for enterprise multi-cluster mesh.
- Helps manage Istio complexity at scale.
- Useful for multi-cloud and platform teams.
Cons
- More advanced than many teams need.
- Requires service mesh and Kubernetes maturity.
- Licensing and architecture should be reviewed carefully.
Platforms / Deployment
Web / Linux-based Kubernetes environments
Cloud / Self-hosted / Hybrid
Security & Compliance
Supports mTLS-based mesh security, policy enforcement, access control, service identity, and centralized governance depending on configuration. Specific compliance certifications should be verified with the vendor.
Integrations & Ecosystem
Gloo Mesh fits organizations using Istio and Envoy across multiple clusters or environments.
- Kubernetes
- Istio
- Envoy proxy
- API gateways
- Observability tools
- GitOps workflows
Support & Community
Gloo Mesh has vendor-backed documentation, enterprise support options, professional services, and ecosystem resources for advanced service mesh users.
#10 — Tetrate Service Bridge
Short description: Tetrate Service Bridge is an enterprise service mesh management and application networking platform built for organizations using Istio, Envoy, and multi-cluster service networking. It focuses on security, governance, and operational control.
Key Features
- Enterprise service mesh management.
- Istio and Envoy-based application networking.
- Multi-cluster and multi-environment service connectivity.
- Zero-trust service access policies.
- Traffic management and resilience controls.
- Observability and service visibility.
- Governance for platform and security teams.
Pros
- Strong for enterprise service mesh governance.
- Useful for complex multi-cluster environments.
- Security-focused approach for service communication.
Cons
- Best suited for mature platform teams.
- May be too advanced for simple Kubernetes environments.
- Cost and implementation effort should be carefully evaluated.
Platforms / Deployment
Web / Linux-based Kubernetes environments
Cloud / Self-hosted / Hybrid
Security & Compliance
Supports mTLS, service identity, access policies, zero-trust controls, traffic governance, and observability depending on configuration. Specific compliance certifications should be verified with the vendor.
Integrations & Ecosystem
Tetrate Service Bridge fits enterprise teams standardizing Istio and Envoy-based networking across clusters and environments.
- Kubernetes
- Istio
- Envoy proxy
- API gateway workflows
- Observability platforms
- Security operations workflows
Support & Community
Tetrate provides enterprise documentation, support, professional services, and expertise around Istio, Envoy, and service mesh operations.
Comparison Table (Top 10)
| Tool Name | Best For | Platform(s) Supported | Deployment | Standout Feature | Public Rating |
|---|---|---|---|---|---|
| Istio | Enterprise Kubernetes service mesh | Kubernetes, Linux-based environments | Cloud / Self-hosted / Hybrid | Deep traffic, security, and policy control | N/A |
| Linkerd | Lightweight Kubernetes service mesh | Kubernetes, Linux-based environments | Cloud / Self-hosted / Hybrid | Simple and lightweight mTLS mesh | N/A |
| Consul Service Mesh | Hybrid service networking | Kubernetes, VMs, Linux environments | Cloud / Self-hosted / Hybrid | Service mesh beyond Kubernetes | N/A |
| Kuma | Multi-zone and universal mesh | Kubernetes, VMs, Linux environments | Cloud / Self-hosted / Hybrid | Kubernetes and universal workload support | N/A |
| AWS App Mesh | AWS-native microservices | AWS workloads, Kubernetes, Linux environments | Cloud | Service mesh for AWS environments | N/A |
| Open Service Mesh | Lightweight Kubernetes mesh | Kubernetes, Linux environments | Cloud / Self-hosted / Hybrid | Open-source Envoy-based mesh | N/A |
| Cilium Service Mesh | eBPF-based Kubernetes networking | Kubernetes, Linux environments | Cloud / Self-hosted / Hybrid | Service mesh with eBPF networking | N/A |
| Traefik Mesh | Simple Kubernetes service mesh | Kubernetes, Linux environments | Cloud / Self-hosted / Hybrid | Lightweight mesh with Traefik ecosystem | N/A |
| Gloo Mesh | Enterprise Istio mesh management | Kubernetes, Linux environments | Cloud / Self-hosted / Hybrid | Multi-cluster Istio management | N/A |
| Tetrate Service Bridge | Enterprise zero-trust service mesh | Kubernetes, Linux environments | Cloud / Self-hosted / Hybrid | Istio and Envoy governance at scale | N/A |
Evaluation & Scoring of Service Mesh Platforms
| Tool Name | Core (25%) | Ease (15%) | Integrations (15%) | Security (10%) | Performance (10%) | Support (10%) | Value (15%) | Weighted Total (0–10) |
|---|---|---|---|---|---|---|---|---|
| Istio | 10 | 6 | 10 | 9 | 8 | 9 | 9 | 8.75 |
| Linkerd | 8 | 9 | 8 | 9 | 9 | 8 | 9 | 8.55 |
| Consul Service Mesh | 9 | 7 | 9 | 9 | 8 | 8 | 8 | 8.35 |
| Kuma | 8 | 8 | 8 | 8 | 8 | 8 | 8 | 8.00 |
| AWS App Mesh | 8 | 8 | 9 | 8 | 8 | 8 | 8 | 8.15 |
| Open Service Mesh | 7 | 8 | 7 | 8 | 8 | 7 | 8 | 7.55 |
| Cilium Service Mesh | 8 | 7 | 8 | 9 | 9 | 8 | 8 | 8.05 |
| Traefik Mesh | 7 | 8 | 7 | 7 | 8 | 7 | 8 | 7.45 |
| Gloo Mesh | 9 | 7 | 9 | 9 | 8 | 9 | 7 | 8.25 |
| Tetrate Service Bridge | 9 | 7 | 9 | 10 | 8 | 9 | 7 | 8.35 |
These scores are comparative and should be used as a decision-support guide, not as a universal ranking. Istio has the deepest ecosystem, while Linkerd is easier for many teams to adopt. Consul and Kuma fit hybrid workloads, Cilium is strong for networking-focused teams, and Gloo Mesh or Tetrate Service Bridge are better suited for enterprise multi-cluster governance.
Which Service Mesh Platform Is Right for You?
Solo / Freelancer
Solo developers usually do not need a full service mesh unless they are learning Kubernetes networking or building advanced microservice demos. Linkerd or Istio can be useful for learning, while lightweight labs can help understand mTLS, routing, and observability concepts.
For simple apps, an ingress controller, API gateway, or basic Kubernetes service networking is usually enough.
SMB
SMBs should prioritize ease of setup, low operational overhead, simple observability, and secure defaults. Linkerd, Traefik Mesh, and Kuma may be easier starting points than heavier enterprise mesh platforms.
If the SMB is already using AWS heavily, AWS App Mesh may be worth evaluating. However, teams should avoid service mesh adoption unless they have enough microservice complexity to justify it.
Mid-Market
Mid-market teams often need stronger traffic control, mTLS, observability, and progressive delivery. Istio, Linkerd, Consul Service Mesh, Kuma, Cilium Service Mesh, and AWS App Mesh can all fit depending on infrastructure and team maturity.
Mid-market buyers should test latency impact, operational complexity, policy configuration, monitoring, GitOps workflows, and rollback behavior before standardizing.
Enterprise
Enterprises should focus on zero-trust networking, service identity, multi-cluster governance, audit visibility, policy consistency, traffic control, observability, and support maturity. Istio, Consul Service Mesh, Gloo Mesh, Tetrate Service Bridge, Cilium Service Mesh, and Kuma are strong enterprise candidates.
Large teams should also standardize ownership between platform engineering, security, SRE, and application teams.
Budget vs Premium
Budget-focused teams can start with open-source options such as Istio, Linkerd, Kuma, Cilium, Traefik Mesh, or Open Service Mesh. However, open-source still requires operational time and expertise.
Premium buyers may consider enterprise platforms such as Gloo Mesh, Tetrate Service Bridge, vendor-supported Consul, or commercial support around Istio and Cilium.
Feature Depth vs Ease of Use
For feature depth, Istio, Gloo Mesh, Tetrate Service Bridge, Consul Service Mesh, and Cilium Service Mesh are strong choices. For ease of use, Linkerd, Traefik Mesh, Kuma, and AWS App Mesh may feel more approachable depending on the environment.
A service mesh should not be selected only because it has many features. It must match the team’s ability to operate it safely.
Integrations & Scalability
Istio has the broadest service mesh ecosystem. Linkerd integrates well with Kubernetes observability workflows. Consul and Kuma work well across Kubernetes and non-Kubernetes environments. AWS App Mesh fits AWS-native workloads. Cilium connects service mesh patterns with modern Kubernetes networking and eBPF-based visibility.
Scalability should be tested using real traffic, real services, deployment frequency, failure scenarios, and observability requirements.
Security & Compliance Needs
Security-focused buyers should evaluate mTLS, service identity, authorization policies, RBAC, audit logs, policy-as-code, ingress and egress control, secrets handling, certificate rotation, and integration with security operations. Regulated organizations should verify vendor documentation and validate configuration patterns before production adoption.
A service mesh can improve security, but poor configuration can also create complexity and hidden risk.
Frequently Asked Questions (FAQs)
1. What is a service mesh?
A service mesh is a dedicated layer that manages communication between services in a microservices environment. It helps with traffic routing, security, observability, and resilience.
2. Why do teams use service mesh platforms?
Teams use service mesh platforms to secure service-to-service traffic, manage routing, apply policies, observe service behavior, and improve reliability in distributed systems.
3. Is service mesh only for Kubernetes?
No. Many service meshes are Kubernetes-focused, but some support virtual machines, hybrid environments, and non-Kubernetes workloads.
4. What is mTLS in service mesh?
mTLS means mutual TLS. It allows services to authenticate each other and encrypt communication between them, helping support zero-trust service networking.
5. Is Istio better than Linkerd?
It depends on the use case. Istio offers deep features and broad ecosystem support, while Linkerd is often simpler and lighter to operate. The best choice depends on team skill and platform needs.
6. Does service mesh replace an API gateway?
No. A service mesh usually manages east-west traffic between services, while an API gateway often manages north-south traffic from users or external clients. Many organizations use both.
7. What are common service mesh mistakes?
Common mistakes include adopting service mesh too early, enabling too many features at once, ignoring performance overhead, weak policy design, poor observability, and unclear ownership between teams.
8. Does service mesh affect performance?
Yes, it can add overhead because traffic may pass through proxies or additional control layers. Teams should test latency, CPU usage, and memory impact before production rollout.
9. What integrations matter most for service mesh?
Important integrations include Kubernetes, observability tools, GitOps platforms, CI/CD pipelines, API gateways, identity systems, certificate management, policy tools, and security monitoring.
10. Is service mesh useful for monolithic applications?
Usually not. Service mesh is most useful when multiple services communicate frequently. Monolithic apps may not benefit enough to justify the added complexity.
Conclusion
Service Mesh Platforms help organizations manage microservice communication with better security, observability, reliability, and traffic control. The best choice depends on architecture, Kubernetes maturity, security requirements, team skill, cloud strategy, and operational complexity. Istio is strong for deep enterprise service mesh use cases, while Linkerd is easier for teams that want a lightweight and simple approach. Consul Service Mesh and Kuma are useful for hybrid workloads, AWS App Mesh fits AWS-centered teams, and Cilium Service Mesh is strong for modern Kubernetes networking. Gloo Mesh and Tetrate Service Bridge support advanced enterprise governance, while Traefik Mesh and Open Service Mesh may fit lighter use cases. The best next step is to shortlist two or three platforms, run a pilot with real services, measure performance overhead, validate mTLS and policy controls, and confirm that the platform improves reliability without adding unnecessary operational burden.Service Mesh Platforms help organizations manage microservice communication with better security, observability, reliability, and traffic control. The best choice depends on architecture, Kubernetes maturity, security requirements, team skill, cloud strategy, and operational complexity. Istio is strong for deep enterprise service mesh use cases, while Linkerd is easier for teams that want a lightweight and simple approach. Consul Service Mesh and Kuma are useful for hybrid workloads, AWS App Mesh fits AWS-centered teams, and Cilium Service Mesh is strong for modern Kubernetes networking. Gloo Mesh and Tetrate Service Bridge support advanced enterprise governance, while Traefik Mesh and Open Service Mesh may fit lighter use cases. The best next step is to shortlist two or three platforms, run a pilot with real services, measure performance overhead, validate mTLS and policy controls, and confirm that the platform improves reliability without adding unnecessary operational burden.